Top 5 Cloud Security Best Practices You Should Follow
Cloud security is an ever-evolving and critically important topic for businesses of all sizes. As more enterprises embrace cloud technologies to drive digital transformation, cloud security best practices become paramount in mitigating cyber risks. With data breaches on the rise, organizations must be more aware of their cloud environments and prioritize security measures. Cloud security best practices, from enforcing access controls and identity management to data encryption and continuous monitoring, help organizations safeguard their sensitive data against emerging threats. However, many companies still struggle to keep up with the latest threats and best practices in cloud security due to the cloud’s complexity and rapid pace of change. In this post, we provide you with an understanding of cloud security best practices that organizations should follow. We will give a detailed overview of techniques that include access controls, identity management, data encryption, threat detection, incident response, and compliance. The information below will help you better secure your cloud and gain peace of mind.
- Implement Strong Identity and Access Management (IAM)
- Encrypt Data at Rest and in Transit
- Conduct Continuous Monitoring and Threat Detection
- Establish a Robust Incident Response Plan
- Maintain Compliance and Regular Security Assessments
- Leverage Cloud Provider Security Features and Shared Responsibility Model
- Use Automation to Enforce Security Policies at Scale
- Secure APIs and Interfaces
- Educate and Train Employees on Cloud Security Awareness
- Backup Data and Plan for Disaster Recovery
- Implement Network Security Controls
- Monitor and Manage Cloud Configuration Settings
- Conclusion
- More Related Topics
Implement Strong Identity and Access Management (IAM)
Identity and Access Management (IAM) is the cornerstone of cloud security, controlling who can access cloud resources and what actions they can perform. Implementing a strong IAM framework is crucial in preventing unauthorized access and data breaches. One of the first steps in this direction is the principle of least privilege, which involves granting users and systems only the minimum access they need to perform their functions. Multi-factor authentication (MFA) is another critical layer that requires users to provide multiple forms of verification before granting access to cloud resources. Role-based access control (RBAC) or attribute-based access control (ABAC) models can help manage access more efficiently by assigning permissions based on user roles or attributes. Regularly reviewing and auditing access permissions and logs can also help identify and rectify potential security gaps.

Encrypt Data at Rest and in Transit
Encryption is a powerful security measure that protects data from unauthorized access by converting it into a format that can only be read with the right decryption key. Encrypting data both at rest (stored data) and in transit (data being transmitted over networks) is essential for protecting sensitive information in the cloud. Many cloud providers offer encryption services, but it’s important to understand how these work and ensure that strong encryption standards are used. Additionally, organizations should implement proper key management practices to secure encryption keys and regularly rotate them.
Conduct Continuous Monitoring and Threat Detection
Continuous monitoring and threat detection are proactive security measures that can help identify and respond to potential threats before they can cause significant damage. This includes real-time visibility into cloud environments, analyzing security logs, and using advanced tools and services for threat detection, such as Security Information and Event Management (SIEM) systems and Intrusion Detection Systems (IDS). Implementing automated alerting mechanisms can help ensure that security teams are immediately notified of potential security incidents. Regular security assessments and penetration testing can also be valuable tools for identifying potential vulnerabilities.
Establish a Robust Incident Response Plan
Despite the best efforts and security measures, security incidents can still occur. Therefore, having a well-defined and tested incident response plan is crucial for minimizing damage and recovery time. The plan should outline roles and responsibilities, steps for identifying, containing, and eradicating threats, and procedures for recovery and post-incident analysis. Regular training and simulations can help ensure that the incident response team is prepared to handle real incidents effectively.
Maintain Compliance and Regular Security Assessments
Compliance with industry standards and regulations is a critical aspect of cloud security, as non-compliance can lead to legal penalties and reputational damage. Regular security assessments and audits are essential to ensure compliance and identify potential security gaps. Vulnerability scanning and penetration testing are proactive security measures that can help identify potential weaknesses in cloud environments. Staying informed about the latest security trends, threats, and best practices is also crucial for maintaining a robust security posture.
Leverage Cloud Provider Security Features and Shared Responsibility Model
Cloud service providers often have robust security features and tools that can be leveraged to enhance cloud security. Understanding the shared responsibility model – the division of security responsibilities between the cloud provider and the customer – is also important. By understanding what aspects of security are covered by the cloud provider and which are the responsibility of the customer, organizations can better allocate their security resources.
Use Automation to Enforce Security Policies at Scale
Automation can be a valuable tool for enforcing security policies across cloud environments at scale. Tools such as Infrastructure as Code (IaC) and security orchestration, automation, and response (SOAR) platforms can help automate security tasks, reduce manual errors, and free up resources for more strategic security work.
Secure APIs and Interfaces
APIs are a common entry point for cloud services, and securing them is an important aspect of cloud security. This includes strong authentication and authorization, regular vulnerability testing, and monitoring API traffic for suspicious activity.
Educate and Train Employees on Cloud Security Awareness
Employees can often be the weakest link in the security chain, and regular security awareness training can help mitigate this risk. Training should cover topics such as recognizing and avoiding phishing attacks, secure password practices, and understanding the organization’s security policies.
Backup Data and Plan for Disaster Recovery
Regular backups and a disaster recovery plan are essential for business continuity in the event of a security incident or other disaster. Backups should be stored securely and tested regularly to ensure that they can be restored successfully.
Implement Network Security Controls
Network security controls such as firewalls, VPNs, and network segmentation can help protect cloud environments from external and internal threats. These controls should be regularly reviewed and updated to adapt to changing threats.
Monitor and Manage Cloud Configuration Settings
Cloud misconfigurations are a leading cause of data breaches, and tools for continuous monitoring and management of cloud configuration settings can help prevent this. This includes tools that can check cloud resources against best practice benchmarks and recommended security configurations.
Conclusion
In today’s rapidly evolving cloud landscape, cloud security is more critical than ever before. Organizations must stay informed about the latest threats and best practices to protect their data and systems from potential cyber attacks. By following the top five cloud security best practices outlined in this blog, you can ensure that your cloud security strategy remains comprehensive, up-to-date, and aligned with your organization’s unique needs. From implementing strong identity and access management (IAM) controls to using automated security solutions and continuously monitoring your cloud environments, these best practices will help you stay one step ahead of cyber threats and protect your valuable data assets.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
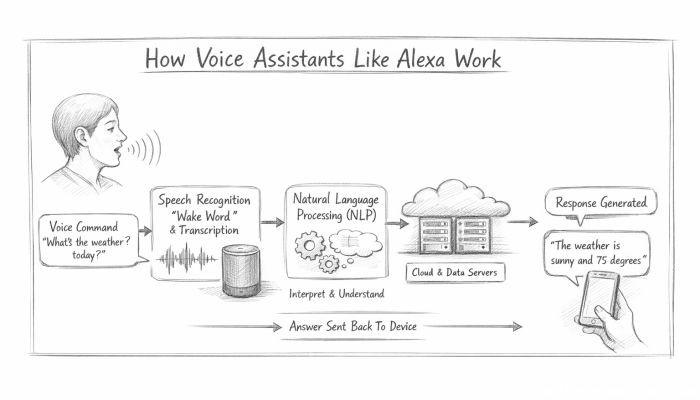 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data