The Importance of Cyber Hygiene and Data Protection
In today's digital era, where information flows seamlessly across networks and devices, safeguarding our digital identity is more crucial than ever. Cyber hygiene and data protection represent a collective set of best practices and strategies designed to shield sensitive information from evolving cyber threats. Whether it’s personal data, corporate secrets, or government information, the increased interconnectivity amplifies vulnerabilities, making effective defenses essential. This article delves deeply into the significance of cyber hygiene and data protection, exploring the threats posed by cyber attacks, practical steps for individuals and organizations to strengthen their defenses, and the broader implications for privacy, trust, and security in the interconnected world. By understanding and implementing robust cyber hygiene principles, everyone can contribute to a safer, more resilient digital environment.
- Understanding Cyber Hygiene: Foundations of Digital Safety
- The Growing Threat Landscape: Why Data Protection Matters
- Data Privacy vs. Data Protection: Clarifying the Differences
- The Role of Strong Password Management
- Software Updates and Patch Management: Closing Vulnerabilities
- Phishing and Social Engineering: Identifying and Avoiding Traps
- Secure Wi-Fi Usage and Network Security
- Data Backup and Recovery: Preparing for the Unexpected
- Mobile Devices and IoT: Expanding the Cyber Hygiene Frontier
- Regulatory Frameworks and Compliance: The Legal Imperative
- Cultivating a Cybersecurity Culture: Education and Awareness
- Future Trends: Evolving Cyber Hygiene in a Changing Digital Landscape
- Conclusion
- More Related Topics
Understanding Cyber Hygiene: Foundations of Digital Safety
Cyber hygiene refers to the routine practices and habits aimed at maintaining the health and security of devices, software, and data within the cyber realm. Much like personal hygiene prevents physical illness, cyber hygiene prevents digital compromises by minimizing vulnerabilities and attack surfaces. This includes regular software updates, password management, awareness about phishing attempts, and cautious browsing behaviors. Emphasizing cyber hygiene is essential because neglected security habits often lead to data breaches or malware infections, which can cascade into severe consequences both personally and professionally.

The Growing Threat Landscape: Why Data Protection Matters
Cyber threats are becoming increasingly sophisticated and prevalent, targeting individuals, businesses, and governments alike. These threats range from phishing schemes and ransomware attacks to state-sponsored espionage. Data protection stands as a critical shield to ensure confidential data—such as financial details, intellectual property, and personal records—does not fall into malicious hands. The financial costs, reputational damages, and legal consequences stemming from data breaches highlight why proactive data protection strategies must be integral to cybersecurity frameworks.
Data Privacy vs. Data Protection: Clarifying the Differences
While often used interchangeably, data privacy and data protection represent distinct but related concepts. Data privacy centers on the right of individuals to control how their personal information is collected, used, and shared. Data protection refers to the technical and organizational measures taken to secure data against unauthorized access or corruption. Understanding this distinction is vital as legislation like GDPR focuses heavily on privacy rights, while data protection involves implementing encryption, secure storage, and access controls to enforce those rights.
The Role of Strong Password Management
Passwords remain the frontline defense against unauthorized access, yet weak or reused passwords contribute heavily to security breaches. Strong password management involves creating complex, unique passwords for each account and updating them regularly. The use of password managers can simplify this process, generating randomized passwords and securely storing them. Multi-factor authentication (MFA) adds an additional layer of security by requiring more than one form of verification, significantly reducing the risk of credential-related attacks.
Software Updates and Patch Management: Closing Vulnerabilities
One of the simplest yet most effective cyber hygiene practices is maintaining up-to-date software and promptly applying security patches. Many cybercriminals exploit known vulnerabilities in outdated systems; by neglecting updates, users effectively leave backdoors open to attackers. This forms an essential part of organizational policies and personal digital routines, ensuring operating systems, applications, and antivirus tools reflect the latest security improvements.
Phishing and Social Engineering: Identifying and Avoiding Traps
Phishing attacks remain one of the most prevalent methods for cybercriminals to gain access to sensitive data by manipulating individuals into revealing credentials or clicking malicious links. Social engineering exploits human psychology rather than technical weaknesses, making awareness training crucial. Recognizing signs of suspicious emails, verifying sender identity, and avoiding unsolicited requests for sensitive information significantly reduce susceptibility to scams.
Secure Wi-Fi Usage and Network Security
Public and unsecured Wi-Fi networks pose considerable risks for data interception and unauthorized access. Cyber hygiene involves connecting only to trusted networks, employing virtual private networks (VPNs) to encrypt data traffic, and disabling automatic connections to unknown networks. For organizations, strategies such as network segmentation, firewalls, and intrusion detection systems form additional layers of network defense.
Data Backup and Recovery: Preparing for the Unexpected
No system is entirely invulnerable to breaches, hardware failures, or accidental deletions. Regular data backups and tested recovery plans ensure that, even if an incident occurs, critical information can be restored quickly with minimal disruption. Best practices recommend maintaining multiple backup copies, including offline and offsite storage, to protect against ransomware attacks that target backup files as well.
Mobile Devices and IoT: Expanding the Cyber Hygiene Frontier
The proliferation of mobile devices and the Internet of Things (IoT) has expanded the cybersecurity perimeter well beyond traditional computers and servers. Mobile phones, smart home devices, and wearable technology all collect and transmit data, forming potential entry points for cyber threats. Applying cyber hygiene to these devices—using strong authentication, keeping firmware updated, and monitoring app permissions—is vital for comprehensive protection.
Regulatory Frameworks and Compliance: The Legal Imperative
Data protection is not only a technical concern but also a legal requirement governed by regulations such as the General Data Protection Regulation (GDPR), California Consumer Privacy Act (CCPA), and others worldwide. Compliance mandates organizations to implement adequate data security measures and respect individual privacy rights, with penalties for non-compliance often severe. Understanding and integrating these legal frameworks into cyber hygiene protocols helps organizations avoid fines and strengthen overall security posture.
Cultivating a Cybersecurity Culture: Education and Awareness
Technology alone cannot guarantee data protection. Cultivating a cybersecurity culture within organizations and communities ensures that every individual understands their role in maintaining security. Continuous education, phishing simulations, clear communication, and incentivizing responsible behavior foster a proactive environment. Awareness reduces human error, which remains one of the leading causes of data breaches.
Future Trends: Evolving Cyber Hygiene in a Changing Digital Landscape
As technology evolves—introducing AI, cloud computing, and quantum computing—the cyber threat landscape will shift dramatically. Cyber hygiene and data protection practices must adapt accordingly, incorporating new tools like biometric authentication, AI-driven threat detection, and zero-trust architectures. Staying informed about emerging threats and innovative defenses will be necessary to maintain resilient cybersecurity in the years ahead.
Conclusion
Cyber hygiene and data protection are indispensable components of digital life, underpinning the security and privacy of individuals and organizations in an increasingly connected world. From strong passwords and software updates to regulatory compliance and awareness training, these practices collectively reduce vulnerabilities and mitigate the impact of cyber threats. As the digital landscape continues to expand and evolve, a commitment to consistent, informed cyber hygiene is vital—not only to safeguard data but also to preserve trust and confidence in technology's role in modern society. Embracing this responsibility at every level empowers us all to navigate the digital world safely and securely.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
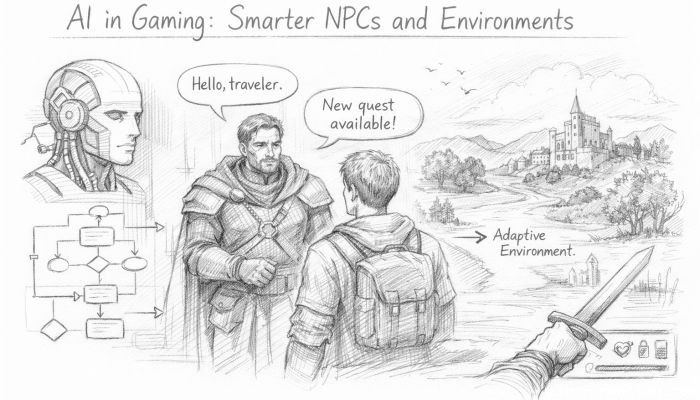 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
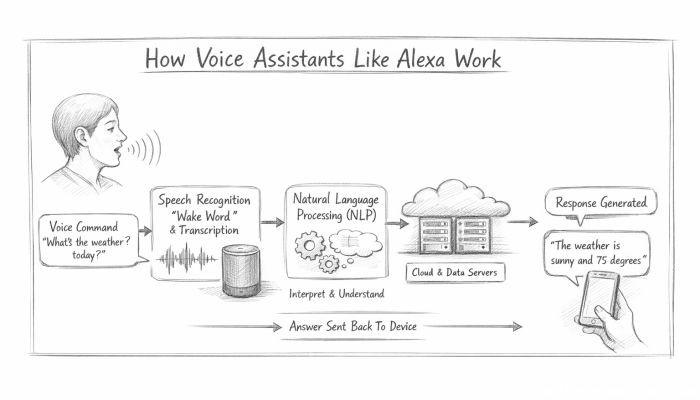 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data