How to Secure IoT Devices
The Internet of Things (IoT) has transformed the way we live, work, and interact with technology by connecting everyday devices—from smart thermostats and wearables to industrial sensors and medical equipment—into a vast, interwoven network. This connectivity creates unprecedented convenience and efficiency but also opens new frontiers for cybersecurity threats. As IoT devices become increasingly integral to personal, corporate, and public infrastructure, securing them has never been more critical. Unlike traditional computers, many IoT devices have limited processing power and memory, which complicates typical security measures. Furthermore, the diversity and sheer number of these devices amplify vulnerabilities, making them prime targets for cyberattacks that can compromise privacy, safety, and even critical systems. This article delves into comprehensive strategies for securing IoT devices, exploring best practices, technological solutions, and emerging trends that foster a safer interconnected environment.
- Understanding the Unique Security Challenges of IoT Devices
- Implementing Strong Authentication and Access Controls
- Keeping Firmware and Software Updated
- Network Segmentation and Secure Communication
- Employing Device Identity and Integrity Verification
- Utilizing IoT Security Gateways and Firewalls
- Monitoring and Anomaly Detection for IoT
- Securing Data Privacy and Handling Sensitive Information
- Establishing Strong Vendor and Supply Chain Security
- Educating Users and Stakeholders About IoT Security
- Incorporating IoT Security into Organizational Policies
- Leveraging Emerging Technologies for Enhanced IoT Security
- Conclusion: Building a Resilient IoT Ecosystem through Comprehensive Security
- More Related Topics
Understanding the Unique Security Challenges of IoT Devices
Before tackling security measures, it’s vital to understand what makes IoT devices uniquely vulnerable. Unlike standard computers or smartphones, many IoT gadgets have minimal computing resources, restricting the ability to implement complex security protocols. Additionally, IoT devices often come with default factory settings and weak or hardcoded passwords, which users may neglect to change, creating easy entry points for hackers. The heterogeneity of manufacturers and communication standards further complicates security management. Many IoT devices store sensitive data or control critical systems, from home security cameras to industrial control units, magnifying the consequences of a breach. Recognizing these challenges highlights the need for specialized security strategies tailored to the constraints and diversity of IoT technology.
Implementing Strong Authentication and Access Controls
Authentication is the first line of defense against unauthorized access. Strong, unique passwords are essential, yet many IoT devices ship with default credentials that often go unchanged. Requiring users to create robust passwords or use passphrases significantly reduces risk. Beyond passwords, employing multi-factor authentication (MFA) adds an additional security layer, requiring users to verify their identities through multiple means such as biometric data or one-time codes. For environments with numerous devices, role-based access controls (RBAC) can ensure that users or systems have only the permissions necessary for their functions, minimizing exposure if credentials are compromised.

Keeping Firmware and Software Updated
Firmware and software updates are vital for patching vulnerabilities as they are discovered. Many IoT devices support over-the-air (OTA) updates to ensure they remain secure over time. Neglecting updates leaves devices open to exploitation through well-known weaknesses. However, updating IoT devices can sometimes be challenging due to limited interfaces or vendor policies. Best practice involves regularly checking for and promptly applying updates, preferably automating the update process when possible. Manufacturers also have a responsibility to provide timely patches and to retire devices no longer supported to prevent them from becoming security liabilities.
Network Segmentation and Secure Communication
IoT devices should not share the same network space with sensitive business or home computers to prevent lateral movement by attackers. Network segmentation, through technologies like virtual LANs (VLANs), separates IoT devices into isolated groups, limiting an attacker’s ability to access other systems after breach. Additionally, all communication to and from IoT devices should be encrypted, commonly using protocols such as TLS (Transport Layer Security). Secure communication prevents interception and tampering with data in transit, which is particularly important for devices handling personal or critical information.
Employing Device Identity and Integrity Verification
Assigning unique cryptographic identities to IoT devices allows systems to verify that only authorized hardware communicates within the network. This can be achieved through digital certificates or secure hardware modules that store cryptographic keys. Integrity verification techniques ensure that device firmware and configurations have not been altered maliciously. Implementing trusted platform modules (TPMs) or secure elements on devices enhances tamper resistance, providing hardware-level security assurances that complement software-driven protections.
Utilizing IoT Security Gateways and Firewalls
Security gateways act as intermediaries between IoT devices and broader networks, managing traffic and enforcing security policies. These gateways can perform deep packet inspection, anomaly detection, and traffic filtering to identify and block suspicious activity. Similarly, specialized firewalls designed for IoT environments regulate inbound and outbound connections according to configured rules, reducing attack surfaces. Employing these centralized security devices simplifies management and enhances visibility into IoT network behavior.
Monitoring and Anomaly Detection for IoT
Continuous monitoring is crucial for early detection of cybersecurity incidents involving IoT devices. Behavioral anomaly detection tools analyze typical device communication patterns and flag unusual activity that may indicate compromise. Real-time monitoring allows prompt response to mitigate potential damage. Security information and event management (SIEM) systems can aggregate and analyze IoT logs alongside other network data for holistic threat detection. Given the scale of IoT deployments, automation and machine learning technologies increasingly play key roles in managing and interpreting the vast data generated.
Securing Data Privacy and Handling Sensitive Information
IoT devices frequently collect sensitive personal or operational data, heightening privacy concerns. To safeguard this information, data should be encrypted both at rest and in transit. Additionally, minimizing data collection to the essentials and applying data anonymization techniques where possible reduces the risk of exposure. Organizations must comply with relevant privacy regulations such as GDPR or HIPAA, ensuring transparent data handling practices and user consent mechanisms. Respecting user privacy fosters trust and reduces legal liabilities.
Establishing Strong Vendor and Supply Chain Security
IoT security starts at the manufacturing stage. Selecting devices from reputable vendors with transparent security policies reduces the likelihood of introducing compromised or vulnerable hardware. Vendors should demonstrate secure development lifecycle practices, vulnerability disclosure programs, and provide timely updates. The supply chain security extends beyond manufacturing to distribution and installation, as tampering during transportation or deployment can introduce risks. Organizations must scrutinize and audit their IoT suppliers and consider security clauses and certifications in procurement contracts.
Educating Users and Stakeholders About IoT Security
Human factors remain one of the weakest links in security. Many users are unaware of the risks associated with IoT devices or how to properly configure and maintain them. Comprehensive education programs targeting end-users, administrators, and decision-makers help promote safe usage habits, such as changing default passwords, recognizing phishing attempts, and promptly installing updates. Awareness campaigns also drive demand for more secure devices, compelling manufacturers to prioritize security features. Training should be ongoing to keep pace with evolving threats and technologies.
Incorporating IoT Security into Organizational Policies
For businesses and institutions utilizing large IoT installations, integrating IoT security into broader information security frameworks is essential. This includes risk assessments, incident response planning, and compliance auditing that specifically address IoT components. Policies should define ownership, responsibility for device management, and protocols for onboarding and decommissioning devices. Coordinated governance reduces security gaps and improves coordinated responses during security incidents. Embedding IoT security in organizational culture strengthens overall cyber resilience.
Leveraging Emerging Technologies for Enhanced IoT Security
The future of IoT security is shaped by emerging technological innovations. Blockchain offers decentralized device authentication and immutable audit trails, improving trustworthiness in distributed environments. Artificial intelligence (AI) enhances threat detection by identifying complex attack patterns across IoT networks. Additionally, advances in hardware security modules and post-quantum cryptography aim to protect IoT devices against evolving cyber threats. Staying current with these technologies enables organizations to build more robust and future-proof IoT ecosystems.
Conclusion: Building a Resilient IoT Ecosystem through Comprehensive Security
Securing IoT devices is an intricate, multifaceted challenge that requires a proactive, layered approach encompassing device, network, user, and organizational dimensions. From enforcing strong authentication and keeping firmware updated to segmenting networks and leveraging advanced monitoring, every step contributes to reducing vulnerabilities inherent in the diverse IoT landscape. Collaboration among manufacturers, users, vendors, and security professionals is vital to foster innovation without compromising safety. As IoT continues to expand dramatically, prioritizing robust security practices not only protects data and infrastructures but safeguards the very trust that underpins the digital age. By adopting best practices and embracing emerging technologies, we can transform the potential pitfalls of IoT into enduring opportunities for secure connectivity.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
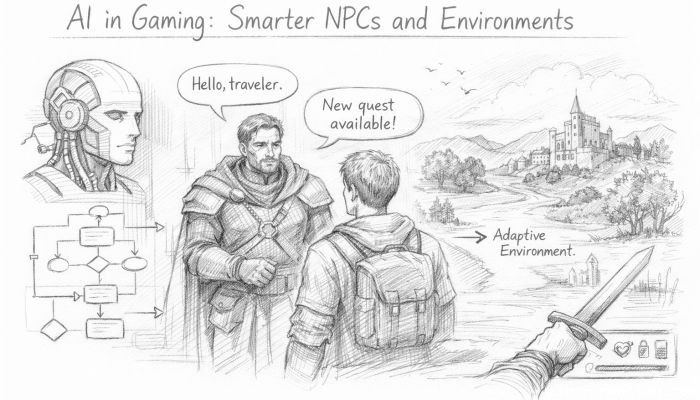 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
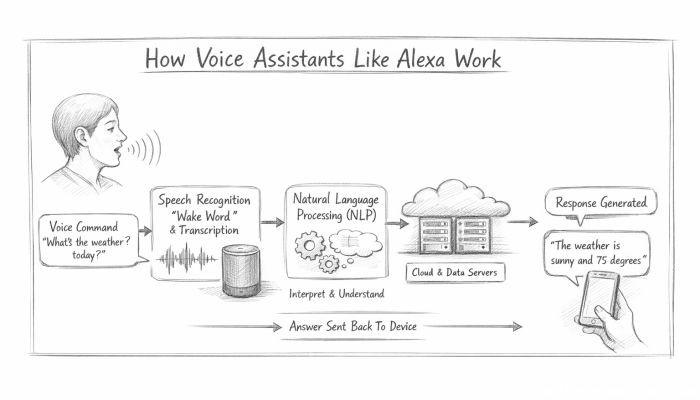 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data