Network Security Fundamentals
In today's interconnected world, the importance of network security cannot be overstated. As organizations and individuals increasingly rely on digital communication and data sharing, the threats to network integrity and confidentiality multiply. Network security fundamentals serve as the foundation for protecting sensitive information, maintaining operational continuity, and safeguarding privacy against cyberattacks. This article delves into the essential concepts, practices, and technologies that form the backbone of network security. From understanding basic threats and vulnerabilities to exploring advanced defense mechanisms, we'll uncover how robust network security frameworks ensure the resilience of our digital infrastructure. Whether you are a beginner or an aspiring professional, this guide offers a comprehensive exploration of the critical components and strategies essential for defending networks in today’s dynamic cyber landscape.
- Understanding Network Security
- Common Threats to Network Security
- The Importance of the CIA Triad
- Network Security Components
- Firewalls: The Gatekeepers of the Network
- Encryption: Securing Data in Transit and at Rest
- Authentication and Access Control
- Intrusion Detection and Prevention Systems (IDS/IPS)
- Network Segmentation and Security Zones
- Security Policies and Employee Training
- Network Security Monitoring and Incident Response
- The Role of Emerging Technologies in Network Security
- Conclusion
- More Related Topics
Understanding Network Security
Network security refers to the policies, practices, and technologies implemented to protect network infrastructure and data from unauthorized access, misuse, malfunction, modification, destruction, or improper disclosure. It encompasses multiple layers of defenses strategically positioned throughout a network to prevent cyber threats. These protections guard network resources such as hardware, software, applications, and data while ensuring confidentiality, integrity, and availability (CIA triad). In essence, network security safeguards the overall digital environment where information flows freely, enabling seamless communication and trustworthy transactions.

Common Threats to Network Security
A fundamental step in securing networks is recognizing the range of threats that compromise network safety. Cyber threats include malware (viruses, worms, trojans), ransomware, phishing attacks, denial-of-service (DoS) attacks, man-in-the-middle (MITM) attacks, and unauthorized access attempts. Each threat targets different vulnerabilities; for example, malware can corrupt files or steal data, whereas DoS disrupts the availability of network services. Attackers continually evolve their approaches, exploiting weaknesses in software, hardware, and human behavior, making it imperative to stay vigilant and adaptive in defensive measures.
The Importance of the CIA Triad
The CIA triad—Confidentiality, Integrity, and Availability—forms the cornerstone of network security. Confidentiality ensures that sensitive information is accessible only to authorized individuals. Integrity guarantees that data remains accurate and unaltered during storage or transmission. Availability means network services and resources are accessible when needed. Effective network security designs aim to balance these three principles, as compromising any one of them can lead to significant consequences like data breaches, financial loss, or operational downtime.
Network Security Components
Network security involves a range of components working together to safeguard the network. Common components include firewalls, intrusion detection systems (IDS), intrusion prevention systems (IPS), antivirus software, virtual private networks (VPNs), and encryption technologies. Firewalls act as a barrier between trusted and untrusted networks, filtering incoming and outgoing traffic. IDS and IPS monitor network activity to detect and prevent suspicious or malicious actions. VPNs encrypt data transmitted across public networks, ensuring privacy and security for remote users.
Firewalls: The Gatekeepers of the Network
Firewalls are one of the most essential tools in network security. They serve as frontline defense, controlling traffic based on predefined security rules. Firewalls can be hardware, software, or a hybrid of both, and they filter traffic by IP addresses, ports, protocols, or application-layer data. Modern firewalls incorporate deep packet inspection and application awareness, providing granular control over network communications. By blocking unauthorized access while allowing legitimate traffic, firewalls help prevent cyber intrusions and data leaks.
Encryption: Securing Data in Transit and at Rest
Encryption transforms readable data into an unreadable format using cryptographic keys, providing confidentiality to sensitive information. It is vital for securing data both in transit across networks and at rest in storage. Protocols like SSL/TLS encrypt web traffic, securing communication between browsers and servers. VPNs use encryption to create secure tunnels for remote connections. Encryption not only protects data from eavesdropping but also maintains integrity and user authentication when combined with digital signatures and certificates.
Authentication and Access Control
Authentication verifies the identity of users or devices attempting to access network resources, while access control determines permissions and restrictions based on roles or policies. Common authentication methods include passwords, biometrics, multi-factor authentication (MFA), and digital certificates. Access control can be implemented as discretionary access control (DAC), mandatory access control (MAC), or role-based access control (RBAC). Proper authentication and access control limit exposure to insider threats and ensure that sensitive systems are accessed only by authorized entities.
Intrusion Detection and Prevention Systems (IDS/IPS)
IDS and IPS are critical for monitoring network traffic and identifying suspicious behaviors indicative of cyber attacks. IDS systems analyze network or system activities and alert administrators about potential threats. IPS, in addition to detection, actively blocks or mitigates malicious actions in real time. By integrating signature-based detection (recognizing known threats) and anomaly-based detection (identifying unusual patterns), IDS and IPS provide layered security capable of responding to evolving threats dynamically.
Network Segmentation and Security Zones
Network segmentation divides a larger network into smaller, isolated segments or security zones, limiting the spread of attacks and reducing risk exposure. Segmentation enables administrators to apply tailored security policies per segment, enhancing control and visibility. Techniques include the use of VLANs (Virtual Local Area Networks), subnetting, and dedicated firewalls between zones. By containing potential breaches within confined areas, network segmentation enhances overall resilience and simplifies threat management.
Security Policies and Employee Training
Strong technical defenses must be complemented by comprehensive security policies and continuous employee education to be effective. Security policies establish formal guidelines for acceptable network use, incident response procedures, and data protection standards. Employee training emphasizes awareness of threats such as phishing, social engineering, and safe handling of credentials. Since human factors often present the weakest link in security, fostering a security-conscious culture within organizations reduces the likelihood of successful attacks.
Network Security Monitoring and Incident Response
Proactive network monitoring allows early detection of anomalies and attacks, facilitating swift incident response. Security Information and Event Management (SIEM) systems correlate logs and alerts from multiple devices, providing actionable insights to security teams. Incident response programs define steps for containment, eradication, recovery, and post-incident analysis. Timely reaction not only minimizes damage but also helps organizations learn from incidents, strengthening their security posture against future threats.
The Role of Emerging Technologies in Network Security
Emerging technologies such as artificial intelligence (AI), machine learning (ML), and blockchain are transforming network security paradigms. AI and ML enable automated threat detection by analyzing massive datasets for subtle indicators of compromise. Blockchain offers decentralized and tamper-proof methods for securing transactions and managing identities. Meanwhile, zero-trust architecture challenges traditional perimeter-based models by enforcing verification at every access point. These innovations, while promising, require thoughtful integration within existing frameworks to maximize benefits.
Conclusion
Network security fundamentals form the critical foundation on which the safety, privacy, and integrity of digital communications rest. By understanding the core principles—such as the CIA triad—and deploying layered defenses involving firewalls, encryption, authentication, intrusion prevention, and segmentation, organizations can build resilient infrastructures capable of withstanding modern cyber threats. Equally important are robust policies, continuous monitoring, agile incident responses, and awareness training that collectively address technical and human vulnerabilities. As cyber threats continue to evolve alongside technological advances, embracing cutting-edge tools like AI and adopting adaptive strategies is essential for sustaining network security in an increasingly digital world. Ultimately, strong network security empowers both businesses and individuals to confidently harness the power of connectivity while protecting what matters most
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
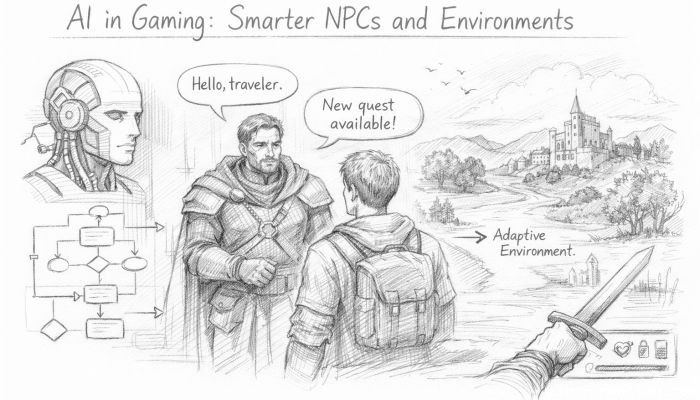 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
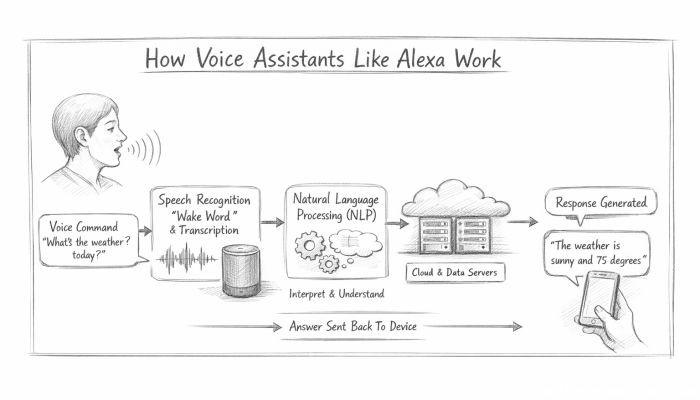 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data