Ethical Hacking vs Black Hat Hacking
In today’s digital age, where information flows seamlessly and the internet is an integral part of personal and professional life, cybersecurity has become a paramount concern. With increasing reliance on technology, the threats posed by malicious cyber activities have grown significantly, making the role of hackers more visible and critical. Hacking itself is a complex phenomenon with two distinct faces: ethical hacking and black hat hacking. While both involve penetrating computer systems and networks, their intent, methods, and consequences differ profoundly. This article delves into the nuanced world of hacking, juxtaposing ethical hacking and black hat hacking, exploring their motivations, techniques, legal implications, and their broader impact on technology and society. By understanding these contrasting practices, readers can better appreciate the fine line between cybersecurity defense and cybercrime.
- Defining Ethical Hacking
- Understanding Black Hat Hacking
- Historical Context of Hacking
- Motivations Behind Ethical Hacking
- Motivations Behind Black Hat Hacking
- Techniques Used in Ethical Hacking
- Techniques Used in Black Hat Hacking
- Legal and Ethical Frameworks
- Impact on Cybersecurity Industry
- Ethical Hacking Career Pathways
- The Dark Side: Consequences of Black Hat Hacking
- Bridging the Gap: White Hat Hackers Turned Black Hats and Vice Versa
- Conclusion
- More Related Topics
Defining Ethical Hacking
Ethical hacking, also known as white hat hacking, refers to the practice of deliberately probing computer systems and networks to identify vulnerabilities before malicious actors can exploit them. Ethical hackers are cybersecurity professionals who work with organizations to strengthen security measures, conduct penetration testing, and develop robust defenses. Their activities are authorized and legal, aiming to protect data integrity and privacy. Ethical hacking serves as a proactive approach to cybersecurity, where the hacker’s role transforms from an adversary to a guardian. By simulating cyberattacks, ethical hackers help organizations understand their weaknesses and patch them to prevent real breaches.
Understanding Black Hat Hacking
In stark contrast, black hat hacking involves unauthorized intrusions into systems for malicious purposes. Black hat hackers exploit vulnerabilities to steal data, disrupt services, spread malware, or cause damage to individuals, companies, or governments. Their motivations range from financial gain, political activism (hacktivism), personal revenge, to sheer mischief. The activities of black hat hackers are illegal and punishable by law, often leading to significant harm both financial and reputational. Unlike ethical hackers, black hats operate outside the law, ignoring ethics or the rights of others, contributing to the shadowy underbelly of cyberspace.

Historical Context of Hacking
The concept of hacking dates back to the early days of computing in the 1960s and 70s, when enthusiasts and researchers explored systems in ways unanticipated by their creators. Initially, hacking was seen as a pursuit of knowledge and innovation rather than crime. However, as technology proliferated and became central to commerce and national security, hacking acquired a dual character. The rise of black hat hacking emerged alongside an increase in cybercrime, data breaches, and hacking scandals. Simultaneously, ethical hacking evolved as a countermeasure, institutionalized with certifications like Certified Ethical Hacker (CEH), advocating responsible exploration of systems.
Motivations Behind Ethical Hacking
Ethical hackers are driven by a commitment to cybersecurity, intellectual challenge, and the goal of making digital environments safer. Many ethical hackers come from a software development or IT background and enjoy problem-solving and uncovering hidden system flaws. Their work contributes to strengthening trust in technology and protecting sensitive information from malicious actors. Ethical hacking often involves collaboration with organizations, governments, and cybersecurity communities, aiming to improve industry standards and resilience against threats.
Motivations Behind Black Hat Hacking
Black hat hackers operate under motivations that are often self-serving or disruptive. Financial incentives are predominant, with hackers engaging in activities like ransomware attacks, identity theft, and financial fraud. Political and ideological motivations can also drive hacking actions, where hackers attempt to expose secrets or topple rivals (a practice sometimes referred to as hacktivism). Some black hats hack for notoriety, thrill-seeking, or as a form of protest. Regardless of motive, black hat hacking generally disregards legal boundaries and ethical concerns, focusing instead on exploiting vulnerabilities for personal or collective gain.
Techniques Used in Ethical Hacking
Ethical hackers employ a variety of sophisticated techniques to test and secure systems. These include penetration testing (pen testing), vulnerability assessments, social engineering simulations, network analysis, and code review. Ethical hackers use tools such as Metasploit, Nmap, and Wireshark to mimic real-world cyberattacks but under controlled conditions. The essence of ethical hacking lies in meticulously documenting findings and offering actionable recommendations to mitigate discovered risks. Through continuous testing and feedback, ethical hackers play a critical role in creating resilient cyber infrastructures.
Techniques Used in Black Hat Hacking
Black hat hackers utilize many overlapping tools and techniques but with malicious intent. Common methods include exploiting software vulnerabilities, phishing scams, malware deployment, denial-of-service (DoS) and distributed denial-of-service (DDoS) attacks, and zero-day exploits. Black hats constantly innovate, developing new malware strains or leveraging social engineering to deceive target users. Unlike ethical hacking, black hat operations prioritize stealth and evasion to maintain access and maximize damage. Their approach often involves hiding identities through proxies, VPNs, or the dark web.
Legal and Ethical Frameworks
The practice of ethical hacking is governed by strict legal and ethical frameworks designed to protect both organizations and hackers. Ethical hackers work under contracts or explicit permissions, ensuring their activities are lawful and transparent. Frameworks like the Computer Fraud and Abuse Act (CFAA) in the U.S. and various international regulations set boundaries on hacking activities. Certification programs and codes of conduct advocate responsible disclosure of vulnerabilities. Conversely, black hat hacking is explicitly illegal under almost all jurisdictions and leads to criminal charges, incarceration, fines, and civil lawsuits. Ethical considerations distinguish the two, emphasizing accountability, consent, and the greater good.
Impact on Cybersecurity Industry
Ethical hacking has become an indispensable component of the cybersecurity industry. Organizations increasingly prioritize hiring ethical hackers or outsourcing penetration testing to identify flaws before breaches occur. This proactive stance has improved security postures and raised awareness about cyber hygiene. Ethical hacking fosters innovation in defense mechanisms, incident response, and recovery strategies. Meanwhile, black hat hacking remains a persistent threat, evolving steadily to challenge security. The ongoing battle between these two forces drives the cybersecurity field’s growth, technological advancement, and policy development.
Ethical Hacking Career Pathways
The rise of ethical hacking has opened numerous career pathways in cybersecurity. Professionals can pursue certifications like CEH, Offensive Security Certified Professional (OSCP), and Certified Information Systems Security Professional (CISSP) to establish credibility. Ethical hackers find roles in corporations, government agencies, security consultancies, and even as independent bug bounty hunters. The demand for white hat hackers continues to grow due to increasing cyber threats and regulatory requirements. Moreover, ethical hacking encourages continuous learning and exposure to cutting-edge technologies and threats, making it a dynamic and rewarding profession.
The Dark Side: Consequences of Black Hat Hacking
Black hat hacking’s consequences extend far beyond the immediate victims. Cyberattacks can lead to massive financial losses, privacy violations, loss of trust, disruption of critical infrastructure, and undermining of national security. High-profile breaches have affected millions of individuals and jeopardized business viability. In some cases, black hat hacking has escalated to cyberwarfare, threatening global stability. These actions also prompt heavier legislation and surveillance, sometimes raising concerns about privacy and civil liberties. The fallout from black hat hacking underscores the importance of robust cyber defenses and the ethical imperative for responsible technology use.
Bridging the Gap: White Hat Hackers Turned Black Hats and Vice Versa
The line between ethical and black hat hacking can sometimes blur, with individuals crossing boundaries due to personal circumstances, ideology, or opportunities. Some hackers begin as black hats but later adopt ethical hacking and aid cybersecurity efforts. Others, disillusioned or tempted by financial gain, may turn rogue. This fluidity highlights the complexity of the hacking world and the significance of ethical grounding and legal adherence. It also emphasizes the need for education, outreach, and support for aspiring hackers to channel their skills positively.
Conclusion
Ethical hacking and black hat hacking represent two polar ends of the cybersecurity spectrum, embodying the ongoing conflict between protection and exploitation in the digital age. Ethical hackers serve as defenders, employing their skills to improve security frameworks, safeguard data, and build trust in technology. Black hat hackers, driven by various motives, exploit vulnerabilities with harmful consequences, challenging the security and stability of digital environments. Understanding the distinctions between these roles, their motivations, techniques, and impacts is crucial for organizations, policymakers, and individuals navigating today’s interconnected world. Ultimately, fostering ethical hacking, supported by clear legal and moral frameworks, is vital for combating cyber threats and ensuring a safer digital future for all.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
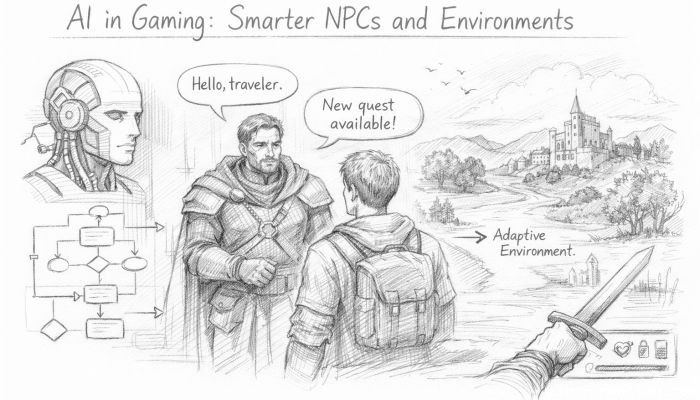 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
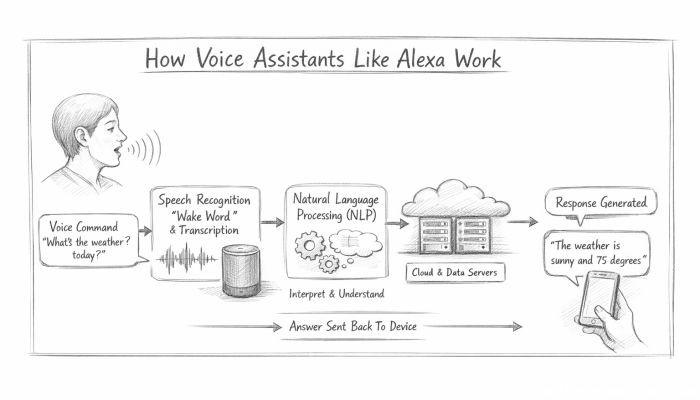 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data