The Future of Quantum Encryption
In an era where data breaches and cyberattacks have become alarmingly frequent, safeguarding sensitive information has never been more critical. Traditional encryption methods, though robust, are increasingly vulnerable to the escalating computational power and advancement of hacking techniques. Enter quantum encryption—a revolutionary approach that leverages the principles of quantum mechanics to create virtually unbreakable security systems. As the quantum revolution gathers momentum, this frontier technology holds the potential to redefine digital security, ensuring privacy in ways previously unimaginable. This article delves into the future of quantum encryption, exploring its principles, current developments, challenges, and implications for a safer digital world.
- Understanding the Basics of Quantum Encryption
- The Role of Quantum Key Distribution (QKD)
- Current State of Quantum Encryption Technology
- Quantum Computers: A Double-Edged Sword
- Practical Applications of Quantum Encryption
- Overcoming the Distance and Infrastructure Limitations
- Integration with Classical Cryptographic Systems
- The Future of Quantum-Resistant Algorithms
- Potential Challenges and Ethical Considerations
- Commercialization and Market Prospects
- Education and Workforce Development in Quantum Security
- Envisioning a Quantum-Secured Digital Future
- Conclusion
- More Related Topics
Understanding the Basics of Quantum Encryption
Quantum encryption, often synonymous with Quantum Key Distribution (QKD), is grounded in the unique properties of quantum mechanics such as superposition and entanglement. Unlike classical encryption, which relies on complex mathematical algorithms, quantum encryption uses the behavior of quantum particles—usually photons—to securely exchange keys. Any attempt at eavesdropping on these quantum keys alters their state, immediately alerting the communicating parties to potential breaches. This property, intrinsic to quantum mechanics, gives quantum encryption a theoretical guarantee of security, making it fundamentally different from and potentially superior to classical encryption techniques.
The Role of Quantum Key Distribution (QKD)
At the heart of quantum encryption lies Quantum Key Distribution. Protocols like BB84, proposed in 1984, demonstrate how two parties can generate a shared, secret key with information-theoretic security. QKD enables the secure transmission of cryptographic keys over quantum channels, typically fiber optics or free space, ensuring that any interception attempts disrupt the quantum states. This disruption is detectable and thus prevents undetected spying, providing a robust foundation for unbreakable communications. As quantum technology matures, QKD is poised to become the cornerstone of secure communications in governments, financial institutions, and industries with critical information.

Current State of Quantum Encryption Technology
Quantum encryption technology has progressed from theoretical frameworks to practical implementations. Leading tech companies and research institutions have developed commercial QKD devices capable of transmitting secure keys over distances reaching hundreds of kilometers. Experimental satellites, such as China’s Micius satellite, have successfully demonstrated space-based quantum communication, extending the reach of quantum encryption beyond terrestrial limitations. However, while these advancements are promising, widespread adoption faces challenges related to cost, infrastructure, and the integration of quantum systems with existing classical networks.
Quantum Computers: A Double-Edged Sword
The emergence of quantum computers presents both risks and opportunities for cybersecurity. On one hand, large-scale quantum computers threaten to break many existing cryptographic schemes like RSA and ECC by efficiently solving problems currently considered intractable. On the other hand, quantum computers enable advanced quantum encryption techniques that could decisively counter these threats. The race is thus two-fold: to develop quantum-resistant algorithms and to harness quantum technologies like QKD to future-proof data security. Understanding this dichotomy is essential to appreciating the urgency and relevance of quantum encryption’s evolution.
Practical Applications of Quantum Encryption
While the theoretical security benefits of quantum encryption are profound, practical applications are beginning to emerge. Governments use encrypted quantum communication channels for diplomatic and military communications to ensure the utmost confidentiality. Financial institutions employ QKD to safeguard sensitive transactions, reducing fraud and unauthorized access. Additionally, sectors such as healthcare, energy, and telecommunications are exploring quantum encryption to protect patient data, control systems, and communication networks from increasingly sophisticated cyber threats. This expanding footprint underscores the technology’s role in protecting critical infrastructure and personal privacy.
Overcoming the Distance and Infrastructure Limitations
One of the significant technical challenges in quantum encryption is the limited transmission distance achievable due to photon loss and signal noise in optical fibers. Current quantum communication links are often limited to a few hundred kilometers without repeaters. However, quantum repeaters—devices that extend quantum signals over longer distances—are under active research and development. The deployment of quantum satellites also offers a solution by facilitating global-scale quantum networks. Building comprehensive quantum communication infrastructure thus involves overcoming physical constraints while integrating these new quantum components with the classical internet.
Integration with Classical Cryptographic Systems
Quantum encryption is not poised to replace classical cryptography overnight but rather to complement it. Hybrid cryptographic systems that combine classical and quantum methods provide a pathway for gradual adoption, balancing performance with enhanced security. For example, quantum keys can be used to periodically refresh classical keys, thus strengthening overall security without abandoning existing cryptographic protocols. Effective integration requires new standards, protocols, and regulatory frameworks to manage the coexistence and interoperability between quantum and classical infrastructures.
The Future of Quantum-Resistant Algorithms
Besides QKD, researchers are actively developing quantum-resistant cryptographic algorithms that can withstand attacks by powerful quantum computers. These post-quantum cryptography (PQC) schemes rely on mathematical problems believed to be resistant to quantum attacks, such as lattice-based cryptography and hash-based signatures. The synergy between quantum encryption and PQC is crucial as quantum hardware matures. While quantum encryption offers unparalleled security for key distribution, PQC algorithms can safeguard stored data and provide broader compatibility across diverse applications, ensuring a multi-layered defense strategy.
Potential Challenges and Ethical Considerations
While quantum encryption promises unprecedented security, it also raises new challenges and ethical questions. The technology could exacerbate inequalities by privileging secure communication to those with access to quantum infrastructure, potentially marginalizing smaller or less wealthy entities. Furthermore, the deployment of quantum networks invites concerns about privacy, control, and the balance of power among states and corporations. Transparency, international cooperation, and the development of ethical standards are imperative to ensure that quantum encryption benefits society broadly and responsibly.
Commercialization and Market Prospects
The quantum encryption market is poised for substantial growth, driven by increasing cybersecurity demands and government investments. Startups, established tech giants, and international alliances are racing to develop scalable and affordable quantum encryption products. Market analysts predict that quantum encryption solutions will become a standard feature in sectors like finance, defense, and telecommunications within the next decade. The commercialization process will likely stimulate innovation, reduce costs, and catalyze the creation of a quantum-secure communication ecosystem accessible to a wider range of users.
Education and Workforce Development in Quantum Security
As quantum technologies evolve, there is growing demand for a skilled workforce capable of designing, implementing, and managing quantum encryption systems. Educational institutions are expanding quantum science and engineering programs, while industry partnerships promote hands-on training and research opportunities. Developing such expertise is essential to transition from experimental technologies to everyday security solutions. A robust quantum cybersecurity workforce will be the backbone of securing digital infrastructure in the quantum era and will drive continuous innovation in this complex and dynamic field.
Envisioning a Quantum-Secured Digital Future
Looking ahead, the fusion of quantum encryption with emerging technologies such as artificial intelligence (AI), blockchain, and Internet of Things (IoT) promises to redefine digital security paradigms. Quantum-secured IoT networks could revolutionize how devices authenticate and communicate, while AI can optimize quantum key management and anomaly detection with unprecedented precision. This confluence will enable resilient, adaptive, and autonomous cybersecurity frameworks capable of countering future threats. The future of quantum encryption is not just about stronger code—it is about fundamentally reshaping the trust architecture of the digital world.
Conclusion
Quantum encryption heralds a new frontier in securing communication, leveraging the strange and powerful phenomena of quantum mechanics to safeguard information against both current and future threats. By fundamentally changing how cryptographic keys are generated and shared, quantum encryption offers information-theoretic security that surpasses the limitations of classical methods. Despite significant technical and practical challenges, ongoing innovations in quantum key distribution, quantum-resistant algorithms, and infrastructure development promise to make quantum encryption an integral component of tomorrow’s cybersecurity landscape. As society embraces this paradigm shift, fostering collaboration, ethical responsibility, and education will be key to unlocking the full potential of quantum encryption and ensuring a secure digital future for all.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
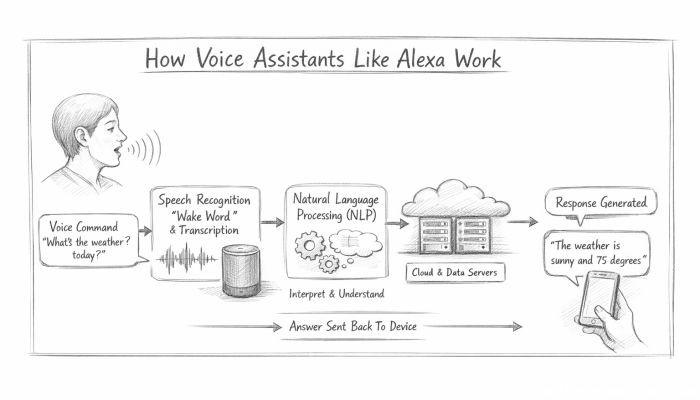 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data