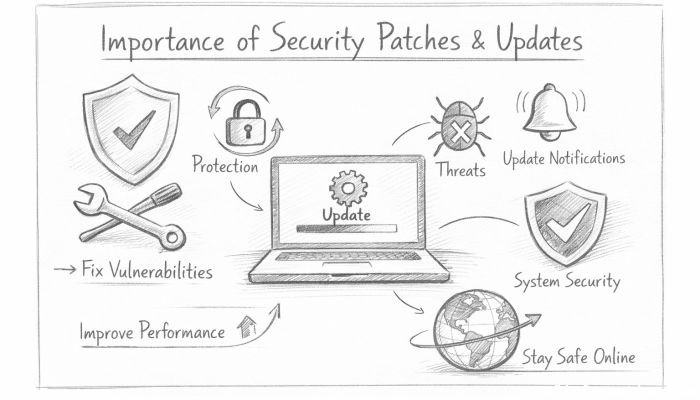
Importance of Security Patches and Updates
In the fast-evolving landscape of technology, security threats are becoming increasingly sophisticated, targeting vulnerabilities in software systems to exploit sensitive information or disrupt services. Whether it’s a smartphone application, enterprise software, or an operating system, vulnerabilities are inevitable due to the vast complexity of modern programs. This is where security patches and updates play a critical role. They serve as the frontline defense mechanism to protect individuals, businesses, and governments from cyberattacks. Understanding the importance of timely installation of security patches and updates is crucial not only for maintaining system functionality but also for safeguarding privacy and data integrity across the digital ecosystem. In this comprehensive article, we will delve into why security patches matter, how they work, and their broader implications in maintaining a secure and resilient technological environment.
- What Are Security Patches and Updates?
- The Nature of Software Vulnerabilities
- The Role of Cyber Threats in Driving Patch Releases
- How Security Patches Protect Data Integrity and Privacy
- Regulatory and Compliance Implications
- The Consequences of Ignoring Security Patches
- Challenges in Patch Management
- The Role of Automation in Efficient Patch Management
- Security Patches in the Era of IoT and Mobile Devices
- Best Practices for Implementing Security Patches
- The Human Factor: User Awareness and Behavior
- The Future of Security Patches and Updates
- Conclusion
- More Related Topics
What Are Security Patches and Updates?
Security patches and updates are software modifications provided by developers to address specific vulnerabilities or bugs identified after the initial release. While a patch targets a particular security flaw, updates often bundle multiple patches along with feature enhancements and performance improvements. These modifications are essential for closing security gaps that malicious actors might exploit. Developers rely on continuous vulnerability assessments—sometimes informed by ethical hackers or user reports—to identify weak points and release patches accordingly. Without these patches, software remains exposed to known exploits, increasing the risk of unauthorized access or data breaches.
The Nature of Software Vulnerabilities
Software vulnerabilities arise due to coding errors, design flaws, or overlooked edge cases during development. Given the complexity of modern software, it is nearly impossible for creators to anticipate every flaw before deployment. Attackers constantly scan software to identify such weaknesses, which can range from simple bugs to critical backdoors permitting full system compromise. Vulnerabilities may also stem from outdated components, third-party libraries, or configuration issues. Recognizing the dynamic nature of threats emphasizes the necessity for ongoing maintenance in the form of patches, effectively turning security into a continuous process rather than a one-time solution.
The Role of Cyber Threats in Driving Patch Releases
Cyber adversaries, including hackers, cybercriminal gangs, and nation-state actors, continuously seek exploitable software vulnerabilities to conduct attacks such as ransomware, data theft, or espionage. Once a vulnerability becomes publicly known, attackers act swiftly to weaponize it before users apply protective patches. This creates a race against time between software vendors deploying patches and attackers launching exploits. The persistent presence of advanced persistent threats (APTs) and automated hacking tools underscores the urgency with which security patches must be developed and disseminated.
How Security Patches Protect Data Integrity and Privacy
Data integrity and privacy are foundational to user trust and regulatory compliance. A compromised system can lead to manipulated data, identity theft, or unauthorized data disclosure. By swiftly addressing exploitative vulnerabilities, security patches prevent attackers from infiltrating systems to alter or steal sensitive information. For organizations, this protection extends to safeguarding customer data, intellectual property, and proprietary information. Failure to patch known vulnerabilities can result in data breaches, which have significant financial, legal, and reputational ramifications.
Regulatory and Compliance Implications
Many industries operate under stringent regulatory frameworks that mandate regular software updates and robust cybersecurity measures. Regulations such as the General Data Protection Regulation (GDPR), Health Insurance Portability and Accountability Act (HIPAA), and Payment Card Industry Data Security Standard (PCI DSS) require entities to protect sensitive data and apply security patches promptly. Noncompliance not only increases vulnerability to attacks but also exposes organizations to hefty fines, legal penalties, and operational disruptions. Proper patch management programs are, therefore, not just technical best practices but legal necessities in many sectors.
The Consequences of Ignoring Security Patches
Delaying or ignoring security patch installations can lead to severe consequences. Cyberattacks exploiting unpatched vulnerabilities have caused some of the most damaging breaches in history, including ransomware infections that paralyze entire networks or malware that siphons off millions of user records. Besides direct financial losses, such incidents erode customer confidence and often require costly remediation efforts. Moreover, negligence in patching may invite regulatory scrutiny and damage brand reputation permanently, undermining years of business development.
Challenges in Patch Management
While the importance of security patches is widely acknowledged, effective patch management faces numerous challenges. These include compatibility issues where patches might disrupt existing applications, operational downtime required during installation, or the complexity of managing large-scale environments with diverse hardware and software assets. Furthermore, the sheer volume of patches released regularly demands dedicated resources to evaluate, test, and deploy updates systematically. Organizations must balance maintaining security with minimizing business disruption—a task that requires careful planning and automation tools.
The Role of Automation in Efficient Patch Management
To address the complexities of patch management, many organizations increasingly leverage automation technologies. Automated patch management tools can scan systems for missing updates, prioritize patches based on threat severity, and schedule deployments with minimal human intervention. This reduces the risk of human error, accelerates response times, and helps maintain consistent compliance with security policies. Automation also enables rapid rollback in case of patch-related issues, ensuring flexibility and business continuity while keeping systems secure.
Security Patches in the Era of IoT and Mobile Devices
The proliferation of Internet of Things (IoT) devices and mobile platforms introduces unique challenges for security patching. Many IoT devices have limited update capabilities or lack mechanisms for automatic patches, leaving them vulnerable to exploitation. Similarly, mobile devices require timely OS and app updates to defend against evolving threats. The expansion of connected devices significantly enlarges the attack surface, making prompt patching essential for protecting not only individual devices but also the broader network environments they operate within.
Best Practices for Implementing Security Patches
Effective patch management involves several best practices that help organizations maintain robust security postures. First, maintaining an up-to-date inventory of all software assets is critical. Prioritizing patches based on risk assessments ensures that critical vulnerabilities are addressed promptly. Testing patches in controlled environments before full deployment prevents disruptions. Regularly scheduled patch cycles, combined with emergency response protocols for zero-day threats, also improve security readiness. Training employees to understand the importance of updates complements technical controls by fostering a security-conscious culture.
The Human Factor: User Awareness and Behavior
Even the most well-developed patches cannot protect systems if end-users ignore update notifications or disable automatic updates due to convenience or misinformation. User education plays a vital role in ensuring patches are applied promptly. Encouraging habits such as backing up data before updates, verifying update sources, and understanding the risks of delaying patches empowers users to actively participate in cybersecurity efforts. Awareness campaigns and clear communication from IT teams or software vendors help bridge the gap between technical measures and user action.
The Future of Security Patches and Updates
Looking ahead, advancements in artificial intelligence (AI) and machine learning are poised to enhance vulnerability detection and patch deployment significantly. Predictive analytics can anticipate emerging threats, enabling proactive patch development. Additionally, the adoption of cloud-native architectures and containers facilitates faster and more frequent update cycles through continuous integration and deployment (CI/CD) pipelines. Nonetheless, the fundamental principle remains unchanged: security patches and updates will continue to be indispensable tools for defending against an increasingly complex threat environment.
Conclusion
Security patches and updates are vital defenses in the perpetual battle against cyber threats. They mitigate risks posed by software vulnerabilities, protect sensitive data, and ensure compliance with regulatory requirements. While challenges in patch management exist, innovations such as automation and AI-driven security are improving capabilities and responsiveness. Importantly, the human factor cannot be overlooked as user awareness and behavior directly influence patch effectiveness. As technology continues to evolve, maintaining a disciplined and proactive approach to patching remains a foundational pillar of cybersecurity. Embracing this ongoing process safeguards not only individual devices and organizations but also the broader interconnected digital infrastructure upon which modern society depends.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
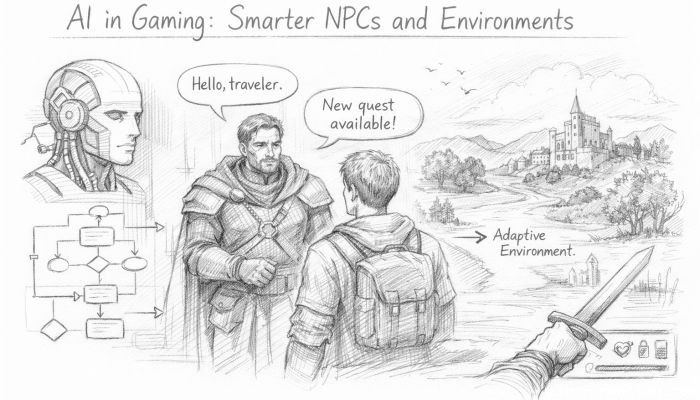 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
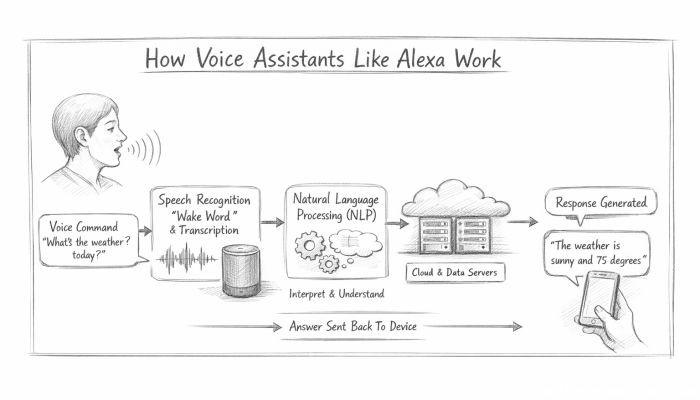 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data