How to Prevent Cross-Site Scripting (XSS)
Cross-Site Scripting (XSS) remains one of the most common and dangerous security vulnerabilities on the web today. This type of attack occurs when malicious scripts are injected into trusted websites, allowing attackers to manipulate client-side scripts and potentially steal sensitive information, hijack user sessions, or deface websites. As web applications grow in complexity and interactivity, the risk of XSS exploits has escalated, making prevention a top priority for developers and security professionals alike. This article delves into the core principles and best practices for preventing XSS attacks, covering essential topics such as input validation, output encoding, content security policies, and modern security frameworks. By understanding and implementing these techniques, developers can vastly reduce the surface area for attacks and ensure safer, more trustworthy web experiences for users.
- Understanding Cross-Site Scripting (XSS)
- The Impact of XSS Attacks on Web Security
- Input Validation: The First Line of Defense
- Output Encoding: Safeguarding Data Display
- Content Security Policy (CSP): A Robust Security Layer
- Using Secure JavaScript Frameworks
- Avoiding Dangerous Functions and Practices
- Sanitization and Escaping Libraries
- Secure Cookie Practices to Minimize Damage
- Regular Security Audits and Penetration Testing
- Educating Developers and Stakeholders on XSS Risks
- Leveraging Web Application Firewalls (WAF)
- Conclusion
- More Related Topics
Understanding Cross-Site Scripting (XSS)
Cross-Site Scripting is a type of injection attack where an adversary injects malicious scripts—typically JavaScript—into webpages viewed by other users. These scripts run in the victim’s browser under the context of the vulnerable site, potentially leading to cookie theft, session hijacking, or unauthorized actions. There are three main types of XSS: Stored (persistent), Reflected (non-persistent), and DOM-based. Stored XSS involves malicious code saved on the target server, while Reflected XSS reflects the malicious input back via URL parameters. DOM-based XSS exploits weaknesses in client-side scripts. Understanding these types is critical to tailoring prevention techniques effectively.
The Impact of XSS Attacks on Web Security
The consequences of XSS attacks can be severe and wide-ranging. Beyond compromising individual users’ data, XSS can erode trust in a website, damage brand reputation, and even result in regulatory penalties if sensitive information is exposed. Attackers using XSS can steal authentication tokens, redirect users to phishing sites, or spread malware. For businesses operating online, these risks translate into financial loss and operational disruption. Therefore, XSS prevention is not just a coding concern but a fundamental element of organizational cybersecurity strategy.

Input Validation: The First Line of Defense
Input validation is the process of ensuring that any data submitted by users meets expected parameters before processing or storage. Effective input validation acts as a filter to block malicious scripts right at entry points. This includes checking for allowed characters, data types, and lengths. However, input validation alone is insufficient to prevent XSS because attackers may find ways to bypass filters or craft inputs that look legitimate. Nonetheless, validating inputs is a foundational step that reduces the risk of harmful data entering the system.
Output Encoding: Safeguarding Data Display
While input validation controls what data enters an application, output encoding controls how data is rendered to users. Output encoding translates special characters into safe representations that browsers interpret as text rather than executable code. For example, converting `<` into `<` prevents the browser from treating malicious input as HTML or JavaScript. Contextual encoding (HTML encoding, JavaScript encoding, URL encoding) is vital—using the correct encoding technique depending on where the untrusted input is inserted (HTML attributes, script blocks, URLs) significantly reduces XSS vulnerabilities.
Content Security Policy (CSP): A Robust Security Layer
Content Security Policy (CSP) is a powerful HTTP header mechanism that helps mitigate XSS risks by restricting the sources from which various types of content (scripts, styles, images) can be loaded. By whitelisting trusted domains and disallowing inline scripts or eval() functions, CSP imposes stringent controls on script execution within the browser. While CSP is not a silver bullet, it provides an effective defense-in-depth layer that limits the impact of potential XSS exploits by containing malicious scripts.
Using Secure JavaScript Frameworks
Modern JavaScript frameworks such as React, Angular, and Vue come with built-in XSS mitigation strategies. These frameworks inherently escape user input when rendering templates, reducing the likelihood of injection vulnerabilities. For instance, React’s JSX automatically escapes variables before rendering, preventing raw HTML injection. Utilizing these frameworks properly and avoiding dangerous functions like `dangerouslySetInnerHTML` or unsanitized `eval()` calls helps maintain security while delivering rich client-side interfaces.
Avoiding Dangerous Functions and Practices
Certain JavaScript functions and coding patterns heighten vulnerability to XSS. Functions like `eval()`, `innerHTML`, and `document.write()` evaluate and insert raw HTML or JavaScript, making them risky when used with untrusted content. Developers should avoid or minimize their use and prefer safer alternatives such as `textContent` or sanitized DOM manipulation libraries. Additionally, embedding user inputs directly into script blocks or HTML without sanitization opens doors to XSS attacks and must be strictly avoided.
Sanitization and Escaping Libraries
Sanitization involves cleaning user input to remove or neutralize risky characters and scripts. Various open-source libraries such as DOMPurify, xss-filters, and OWASP Java HTML Sanitizer offer tested solutions for sanitizing inputs and outputs. These libraries help enforce rigorous content filtering and encoding that can be complex to implement manually. Using such vetted tools ensures consistent sanitization while adhering to evolving attack vectors and best security practices.
Secure Cookie Practices to Minimize Damage
Cookies often store session tokens and authentication data. Securing cookies with flags like HttpOnly and Secure helps reduce the damage caused by potential XSS attacks. The HttpOnly flag prevents JavaScript access to cookies, thus hindering theft through XSS. The Secure flag ensures cookies are only sent over encrypted HTTPS connections. Although these measures do not prevent XSS itself, they mitigate critical consequences such as session hijacking.
Regular Security Audits and Penetration Testing
Even with robust preventive coding, continuous security auditing and testing are essential. Manual code reviews, static analysis tools, and automated scanners help identify potential XSS vulnerabilities early. Penetration testing simulates real-world attack scenarios and uncovers hidden weaknesses in web application logic. Integrating security testing into the development lifecycle accelerates detection and remediation of vulnerabilities, keeping applications resilient against emerging XSS techniques.
Educating Developers and Stakeholders on XSS Risks
Human error remains a significant factor in security breaches, including XSS. Training developers on secure coding practices, understanding XSS mechanisms, and the importance of following preventive protocols is essential. Similarly, raising awareness among product owners and project managers ensures security priorities are aligned with business objectives. Cultivating a security-first mindset fosters a proactive approach to detecting and preventing XSS vulnerabilities from the design phase to deployment.
Leveraging Web Application Firewalls (WAF)
Web Application Firewalls act as an additional protective barrier by filtering and monitoring incoming traffic for malicious payloads, including XSS attack patterns. Although WAFs should not replace secure coding, they offer an important supplementary defense by detecting and blocking many common attack vectors in real time. Implementing properly configured WAFs helps organizations rapidly respond to and mitigate attempts to exploit XSS flaws during runtime.
Conclusion
Preventing Cross-Site Scripting is a multifaceted challenge that demands diligent attention across the entire web development lifecycle. From input validation and output encoding to the use of Content Security Policies and safe JavaScript practices, robust defense in depth is essential to thwart these pervasive attacks. Complementing secure coding with tools like sanitization libraries, security testing, and Web Application Firewalls strengthens protection even further. As attackers continuously evolve their techniques, maintaining a proactive and informed security posture will be crucial in safeguarding users, preserving trust, and ensuring resilient web applications. Ultimately, effective XSS prevention is a collective effort combining technical rigor, ongoing education, and strategic foresight to build a secure digital future.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
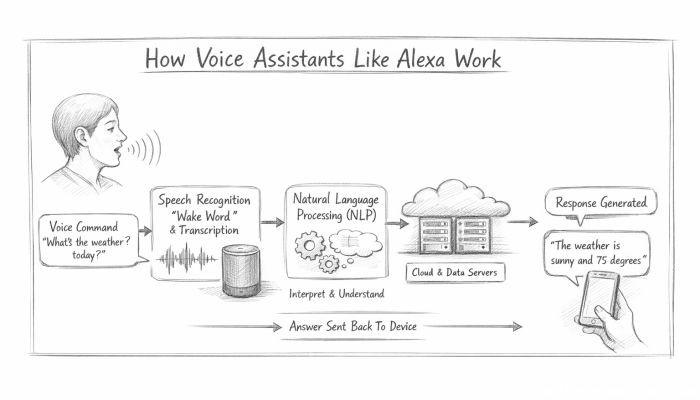 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data