How Hackers Exploit SQL Injection
In today’s digital era, where data reigns supreme, the security of databases has become a critical concern for organizations and individuals alike. Among various cyber threats, SQL Injection remains one of the most notorious and prevalent attack vectors that hackers exploit to infiltrate systems and compromise sensitive data. This technique exploits vulnerabilities in poorly coded web applications, allowing attackers to interfere with the queries an application makes to its database. Understanding how hackers execute SQL Injection attacks is essential not only for cybersecurity professionals but also for developers, businesses, and anyone involved in managing web-based systems. This article dives deep into the mechanisms of SQL Injection, how attackers leverage it to breach systems, the various forms it takes, and the strategies to protect against such intrusions.
- What is SQL Injection?
- The Mechanics of SQL Injection Attacks
- Types of SQL Injection Attacks
- Common Vulnerabilities Exploited by Hackers
- How Attackers Discover SQL Injection Points
- Exploitation Techniques: From Data Retrieval to System Control
- The Role of Automated Tools in SQL Injection Attacks
- Impact of SQL Injection on Businesses and Individuals
- Preventing SQL Injection: Best Coding Practices
- Role of Web Application Firewalls (WAFs) and Security Tools
- SQL Injection and Emerging Technologies
- Case Studies Highlighting SQL Injection Exploits
- Conclusion
- More Related Topics
What is SQL Injection?
SQL Injection (SQLi) is a code injection technique in which an attacker inserts malicious SQL statements into an entry field for execution by the back-end database. This manipulation occurs because the application does not properly sanitize user input, leading to unexpected SQL commands that the database then executes. Essentially, SQLi exploits vulnerabilities in the interface between web applications and databases, enabling attackers to interfere with the underlying queries, retrieve unauthorized information, or even alter or delete data.
The Mechanics of SQL Injection Attacks
The attack typically begins when a hacker identifies an input field—such as a login form or search box—where user data is directly embedded into an SQL query without adequate validation. By inputting specially crafted SQL code, the attacker can manipulate the query’s logic. For example, instead of entering a username, an attacker might input `' OR '1'='1` which tricks the database into always returning true, thereby bypassing authentication. The underlying issue is the application's failure to distinguish code from data, allowing injection of executable commands.

Types of SQL Injection Attacks
Hackers employ various forms of SQL Injection based on the target system's design and the nature of its database.
- Classic SQL Injection: Involves inserting malicious queries directly into an input field.
- Blind SQL Injection: When error messages are suppressed, hackers infer data by analyzing response behaviors.
- Error-Based SQL Injection: Exploits detailed database error messages to gather information.
- Union-Based SQL Injection: Uses the UNION SQL operator to combine results from multiple queries.
- Second-Order SQL Injection: Payloads stored to be executed later, exploiting stored procedures or delayed logic.
Each variation allows attackers different avenues to extract information or manipulate data.
Common Vulnerabilities Exploited by Hackers
Critical to SQL Injection’s success are weaknesses within the application's coding practices. These include:
- Lack of input validation
- Inadequate or absent use of parameterized queries
- Reliance on dynamic SQL queries constructed through string concatenation
- Detailed database error disclosures
- Poor configuration or outdated database management systems
Hackers scan for these vulnerabilities through automated tools and manual testing, targeting the weakest links to gain unauthorized access.
How Attackers Discover SQL Injection Points
Identifying injection points is a critical phase in an attacker’s process. Hackers use automated scanners and fuzzers that send a variety of input payloads designed to provoke errors or unexpected behavior in an application. If the system responds with errors or returns certain logical outputs, it signals an injection vulnerability. Manual probing includes inserting special characters such as quotes, semicolons, or SQL keywords to observe the application's reactions. This reconnaissance enables attackers to map out where and how SQL Injection can succeed.
Exploitation Techniques: From Data Retrieval to System Control
Once a vulnerability is found, attackers can exploit it for various malicious purposes:
- Data Extraction: Accessing user information, credentials, payment details, or proprietary data.
- Authentication Bypass: Logging in as an administrator without valid credentials.
- Data Manipulation: Modifying or deleting existing database records.
- Denial of Service: Crafting queries that overload or crash the database.
- System Compromise: In advanced cases, injection leads to shell commands execution or ransomware deployment.
This broad spectrum of damage shows why effective SQL Injection mitigation is non-negotiable.
The Role of Automated Tools in SQL Injection Attacks
Hackers increasingly depend on sophisticated automated tools such as SQLMap and Havij that simplify identification, exploitation, and data extraction in injection attacks. These tools can automate the entire attack cycle—scanning for injection points, enumerating databases and tables, extracting data, and sometimes even modifying data or writing backdoors. Their efficiency makes SQL Injection a favorite technique among both opportunistic hackers and advanced persistent threats, dramatically increasing the scale and speed of attacks.
Impact of SQL Injection on Businesses and Individuals
The consequences of SQL Injection attacks are significant and wide-ranging. For businesses, data breaches lead to financial loss, reputational damage, legal liabilities, and regulatory penalties, especially under frameworks like GDPR and HIPAA. Individuals may suffer identity theft, financial fraud, and privacy violations. High-profile breaches often trace back to SQL Injection flaws, underscoring the vital importance of robust database and application security.
Preventing SQL Injection: Best Coding Practices
Defense begins at the development stage. Secure coding practices include:
- Employing prepared statements or parameterized queries that separate code from data.
- Using stored procedures with strict input controls.
- Implementing rigorous input validation and sanitization.
- Avoiding dynamic SQL or carefully escaping all inputs.
- Limiting database permissions to minimize damage scope.
- Regular code reviews and security testing.
Adherence to these practices significantly reduces injection risks.
Role of Web Application Firewalls (WAFs) and Security Tools
In addition to secure coding, security layers such as Web Application Firewalls serve as effective barriers by detecting and blocking malicious SQL payloads. WAFs analyze incoming traffic patterns, filter suspicious characters, and provide real-time mitigation against injection attempts. Combined with regular vulnerability scanning and penetration testing, these tools form critical defenses against evolving injection-based threats.
SQL Injection and Emerging Technologies
With the rise of cloud databases, microservices, and API-driven architectures, SQL Injection adaptation has evolved. Attackers now target APIs that interface with databases, or misconfigured cloud storage. Additionally, the integration of NoSQL databases has introduced variations of injection attacks that mimic SQLi principles in different query languages. Hence, security approaches must evolve in tandem with technology advancements, ensuring comprehensive protection in modern environments.
Case Studies Highlighting SQL Injection Exploits
Examining real-world incidents provides valuable insights. For instance, the 2017 Equifax breach stemmed partly from SQL Injection vulnerabilities, exposing sensitive data of millions. Similarly, SQL Injection was the entry point in attacks against TalkTalk and Sony Pictures, leading to massive data and intellectual property losses. These cases demonstrate how neglecting SQL Injection defenses can lead to devastating outcomes, serving as cautionary tales for all stakeholders.
Conclusion
SQL Injection remains a potent and pervasive cyber threat because it preys on fundamental software development oversights. By exploiting unvalidated user inputs, attackers can manipulate database queries to access, alter, or destroy critical information. Understanding the anatomy of SQL Injection attacks—from discovery and execution to impact and prevention—is essential in fortifying digital defenses. Developers must embrace secure coding standards, organizations should deploy layered security controls, and continuous vigilance is indispensable in the evolving landscape of cyber threats. While technology advances, the core lesson remains unchanged: robust input validation, prudent database permissions, and proactive defense strategies are the keystones to mitigating SQL Injection’s destructive potential and safeguarding data integrity.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
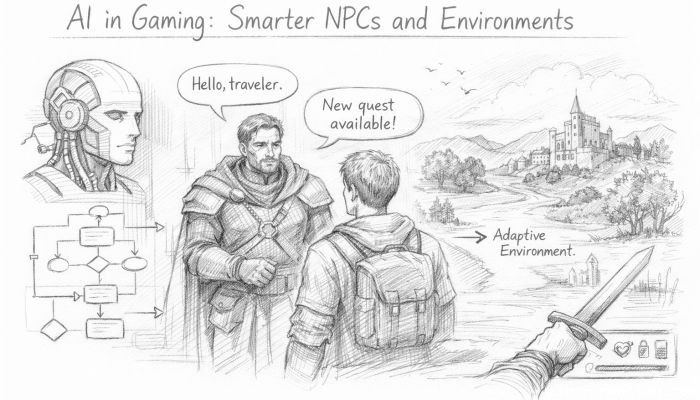 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
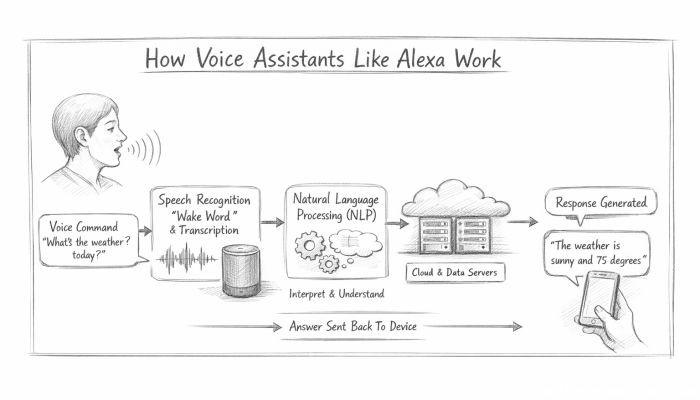 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data