Introduction to Penetration Testing
In today’s digital age, where information is one of the most valuable commodities, securing digital assets has become paramount for individuals, organizations, and governments alike. Cyber threats are increasingly sophisticated, and vulnerabilities within software, hardware, and human processes can be exploited with devastating consequences. Penetration testing, often referred to as ethical hacking, has emerged as a critical practice that helps identify security weaknesses before malicious actors can exploit them. This proactive approach to cybersecurity involves simulating real-world attacks on systems, networks, and applications to evaluate their defenses. In this comprehensive article, we will explore the fundamentals of penetration testing, its methodologies, tools, and best practices. Whether you are a beginner eager to understand the basics or a professional seeking to enhance your security skills, this introduction will guide you through the essential aspects of penetration testing.
- What is Penetration Testing?
- The Importance of Penetration Testing
- Types of Penetration Testing
- Phases of Penetration Testing
- Tools Used in Penetration Testing
- Common Vulnerabilities Exploited by Penetration Testers
- Legal and Ethical Considerations
- Penetration Testing vs. Vulnerability Scanning
- Challenges in Penetration Testing
- The Role of Automation and AI in Penetration Testing
- Penetration Testing Methodologies and Frameworks
- Getting Started with Penetration Testing: Skills and Training
- Conclusion
- More Related Topics
What is Penetration Testing?
Penetration testing (often abbreviated as “pen testing”) is a controlled and authorized process of probing computer systems, networks, or applications to identify security vulnerabilities that attackers could exploit. Unlike other forms of vulnerability assessment that merely report weaknesses, penetration testing attempts to exploit these weaknesses to demonstrate their existence and potential impact. This hands-on simulated attack helps organizations understand how an adversary could breach their defenses and gain unauthorized access, thereby enabling them to take corrective measures before a real attack occurs.
The Importance of Penetration Testing
Modern organizations rely heavily on technology for daily operations, making them prime targets for cybercriminals. Penetration testing is a critical component of an organization’s security posture because it reveals hidden vulnerabilities that automated scans might miss. By identifying and exploiting security gaps, pen testers help organizations prioritize fixes, reduce risk, and comply with regulatory requirements such as PCI-DSS, HIPAA, and GDPR. Moreover, pen testing enhances the overall security culture by raising awareness among IT staff and management about potential threats.

Types of Penetration Testing
There are several types of penetration tests based on scope and methodology. Black-box testing involves minimal or no prior knowledge of the system, resembling an external attacker’s approach. White-box testing, in contrast, provides the tester with detailed internal information such as source code, system architecture, and credentials, representing a knowledgeable insider’s perspective. Grey-box testing blends these two, with limited knowledge shared before the test. Additionally, penetration tests can target specific layers such as network, web application, mobile, wireless, or social engineering, each focusing on different attack vectors.
Phases of Penetration Testing
Penetration testing follows a structured lifecycle to ensure thorough and systematic assessment. The process typically begins with planning and reconnaissance, during which testers gather information about the target system. The next phase is scanning, where automated tools scan for vulnerabilities. The gaining access phase involves exploiting identified weaknesses to enter the system. Testers then maintain access briefly to assess potential for deeper infiltration, followed by analysis and reporting, which details vulnerabilities found, exploits used, and recommended mitigations. This methodical approach ensures comprehensive coverage and actionable outputs.
Tools Used in Penetration Testing
Penetration testers use a variety of tools to automate and facilitate the identification and exploitation of vulnerabilities. Popular tools include Nmap for network mapping and port scanning, Metasploit for exploiting vulnerabilities and payload delivery, Burp Suite for web application testing, and Wireshark for network traffic analysis. Additionally, specialized tools exist for password cracking, wireless attacks, and social engineering simulation. Mastery of these tools, combined with creativity and technical knowledge, is essential for effective penetration testing.
Common Vulnerabilities Exploited by Penetration Testers
Penetration testers focus on uncovering a wide range of vulnerabilities, including outdated software with known exploits, weak or default passwords, misconfigured firewalls, and insecure coding practices such as SQL injection and cross-site scripting (XSS). Social engineering tactics target human weaknesses, tricking employees into revealing credentials or clicking malicious links. Another frequent area is unpatched systems that have known security flaws actively exploited in the wild. Identifying these vulnerabilities helps organizations implement stronger controls and patch management policies.
Legal and Ethical Considerations
Due to the potential risks associated with penetration testing—such as data loss, system crashes, or exposure of sensitive information—it is imperative to conduct tests within clear legal and ethical boundaries. Penetration tests must have explicit written permission and well-defined scope from the target organization. Testers should comply with applicable laws like the Computer Fraud and Abuse Act (CFAA) and respect privacy principles. Ethical conduct also involves responsible disclosure of findings and collaboration to remediate vulnerabilities, ensuring the testing activity enhances security without causing harm.
Penetration Testing vs. Vulnerability Scanning
Although related, penetration testing and vulnerability scanning serve distinct functions. Vulnerability scanning uses automated tools to quickly identify known security issues in systems without attempting to exploit them. It offers breadth but limited depth. Penetration testing is more thorough and interactive, involving actual exploitation attempts to validate vulnerabilities and assess business impact. While vulnerability scanning is suitable for routine security checks, penetration testing is essential for deeper analysis, particularly before major deployments or compliance audits.
Challenges in Penetration Testing
Penetration testing is a complex and resource-intensive activity that faces several challenges. One major hurdle is the dynamic nature of IT environments; new vulnerabilities emerge constantly, and maintaining an up-to-date understanding of threats requires continuous learning. Testers must balance thoroughness with minimizing disruptions to live operations. Additionally, some vulnerabilities may be difficult to exploit without risking system stability. Communication between testers and stakeholders can also be challenging, requiring clear explanation of technical findings in business terms.
The Role of Automation and AI in Penetration Testing
Advancements in automation and artificial intelligence (AI) are transforming the penetration testing landscape. Automated tools can run repetitive tasks faster, such as scanning and basic exploitation attempts, freeing testers to focus on complex scenarios. AI-powered systems analyze massive datasets to identify emerging threats and suggest novel attack vectors. However, human ingenuity remains essential for interpreting results, crafting sophisticated exploits, and understanding context-specific risks. The future of penetration testing likely includes hybrid approaches combining automation's efficiency with expert judgment.
Penetration Testing Methodologies and Frameworks
Several established methodologies guide penetration testers to systematically conduct assessments. Examples include the Open Web Application Security Project (OWASP) Testing Guide for web applications, the Penetration Testing Execution Standard (PTES), and the NIST SP 800-115 technical guide to information security testing. These frameworks provide best practices, checklists, and structured approaches to ensure consistency, completeness, and quality in testing. Adhering to recognized methodologies also helps organizations align penetration testing efforts with industry and regulatory standards.
Getting Started with Penetration Testing: Skills and Training
For individuals interested in pursuing penetration testing, building a strong foundation is essential. Key skills include networking fundamentals, operating system knowledge (especially Linux and Windows), programming and scripting languages such as Python or PowerShell, and familiarity with security concepts and protocols. Practical experience with common tools and virtual labs enhances learning. Certifications such as Certified Ethical Hacker (CEH), Offensive Security Certified Professional (OSCP), and GIAC Penetration Tester (GPEN) validate expertise and are highly regarded in the industry.
Conclusion
Penetration testing is a vital practice in the ongoing battle against cyber threats, providing invaluable insights into an organization’s security posture by proactively uncovering vulnerabilities and demonstrating their real-world impact. Through carefully planned and executed simulated attacks, penetration testers help organizations identify weaknesses, prioritize remediation, and strengthen defenses. While the landscape of cyber threats continues to evolve rapidly, the fundamentals of penetration testing—combining technical skill, strategic thinking, and ethical conduct—remain essential. As technologies advance and new tools emerge, penetration testing will continue to play a crucial role in safeguarding digital assets and fostering a resilient cybersecurity environment. For those entering this field, a commitment to continuous learning and adherence to ethical standards will unlock promising opportunities in one of the most challenging and rewarding areas of IT security.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
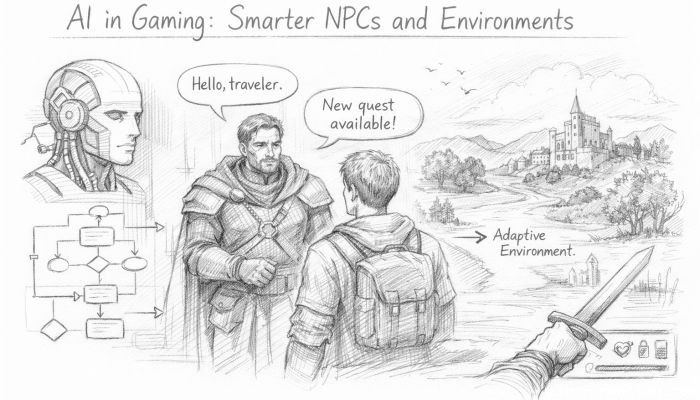 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
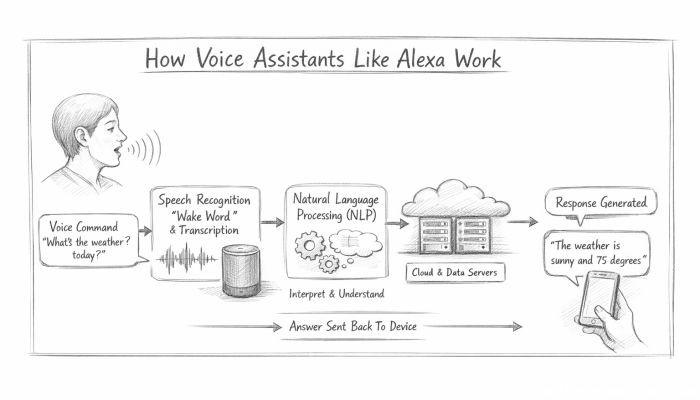 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data