Basics of Ethical Hacking
In today’s digitally interconnected world, cybersecurity stands as a paramount concern for individuals, organizations, and governments alike. With cybercrime growing in scale and complexity, protecting sensitive information and digital infrastructure has never been more critical. Ethical hacking, sometimes known as white-hat hacking, represents a proactive approach to cybersecurity — one that anticipates vulnerabilities before malicious actors exploit them. This discipline involves authorized, deliberate attempts to breach systems to identify weaknesses and recommend improvements. This article delves into the fundamentals of ethical hacking, providing a comprehensive overview of its principles, methodologies, and significance in safeguarding our digital environment. Whether you’re a budding cybersecurity professional or simply curious about the mechanics of hacking for good purposes, understanding ethical hacking is an essential step in appreciating how security in the modern age is maintained.
- Understanding Ethical Hacking: Definition and Purpose
- The Role of Ethical Hackers in Cybersecurity
- Types of Ethical Hackers: White Hat, Black Hat, and Grey Hat
- Key Skills and Knowledge Areas for Ethical Hackers
- Common Tools Used in Ethical Hacking
- Types of Ethical Hacking Techniques
- The Ethical Hacking Process: Phases and Methodology
- Legal and Ethical Considerations
- Certification and Career Pathways in Ethical Hacking
- The Importance of Ethical Hacking for Organizations
- Challenges Faced in Ethical Hacking
- Future Trends in Ethical Hacking
- Conclusion
- More Related Topics
Understanding Ethical Hacking: Definition and Purpose
Ethical hacking refers to the practice of intentionally probing computer systems, networks, or applications to uncover security vulnerabilities that could be exploited by hackers. Unlike malicious hacking, ethical hacking is conducted with explicit permission from the system owners and follows strict legal and ethical guidelines. The primary goal is to identify weak spots that may allow unauthorized access, data breaches, or other forms of cyberattacks. Ethical hackers then provide comprehensive reports and recommendations to strengthen the security posture of the systems they test, thus helping prevent cybercrime and maintaining trust in digital technologies.

The Role of Ethical Hackers in Cybersecurity
Ethical hackers play an indispensable role in modern cybersecurity by acting as the first line of defense. They simulate the tactics, techniques, and procedures of real attackers but with the ultimate aim of pinpointing and addressing flaws beforehand. By thinking like hackers, ethical hackers help organizations anticipate potential threats, ensuring that their defenses are robust and up-to-date. In many ways, they function both as detectives and consultants, combining technical expertise with strategic insight to counteract cyber threats.
Types of Ethical Hackers: White Hat, Black Hat, and Grey Hat
Understanding ethical hacking also involves distinguishing between the types of hackers based on intent and authorization. White hat hackers are ethical professionals who work within legal boundaries to protect systems. Black hat hackers, on the opposite end, are cybercriminals who exploit vulnerabilities for malicious purposes such as theft or disruption. Grey hat hackers operate in a legal and moral gray area; they might discover vulnerabilities without permission but usually report them without causing harm. Ethical hacking is firmly rooted in white hat activities, emphasizing integrity and the well-being of users.
Key Skills and Knowledge Areas for Ethical Hackers
Ethical hackers must master a broad spectrum of technical and analytical skills. Knowledge in computer networking, operating systems, programming languages, and security protocols is fundamental. Familiarity with tools like penetration testing software, vulnerability scanners, and cryptography enhances their ability to detect and exploit system weaknesses effectively. Beyond technical acumen, ethical hackers need sharp problem-solving skills, creativity to think like attackers, and a strong ethical compass to ensure their work complies with legal standards.
Common Tools Used in Ethical Hacking
Toolsets are vital to ethical hacking, enabling practitioners to efficiently test systems and analyze vulnerabilities. Popular tools include Nmap for network scanning, Metasploit for exploiting software vulnerabilities, Wireshark for traffic analysis, and Burp Suite for web application security testing. Each tool serves a unique purpose, from reconnaissance and scanning to gaining access and maintaining persistence on a system. Mastery of these tools — alongside manual techniques — is essential for effective ethical hacking.
Types of Ethical Hacking Techniques
Ethical hacking uses various techniques to probe system defenses. These include reconnaissance (gathering information about targets), scanning (identifying open ports and services), gaining access (exploiting vulnerabilities), maintaining access (ensuring continued presence), and covering tracks (erasing evidence of the testing process). Techniques such as social engineering, password cracking, SQL injection, and phishing simulations are also employed to test human and technological defenses alike.
The Ethical Hacking Process: Phases and Methodology
Ethical hacking typically follows a systematic process that ensures thorough and responsible testing. It begins with planning and reconnaissance to gather relevant information. Next comes scanning to identify vulnerabilities, followed by the exploitation phase where hackers attempt to breach the system. After successfully gaining access, they evaluate how deep the breach can go, then document their findings comprehensively. The final phase involves reporting and remediation suggestions. This structured approach guarantees clarity, accountability, and maximizes security improvements.
Legal and Ethical Considerations
Ethical hacking operates within a well-defined legal framework emphasizing explicit consent and respect for privacy. Conducting any hacking activity without permission is illegal and punishable under cybersecurity laws worldwide. Ethical hackers must adhere to strict guidelines, ensuring transparency, confidentiality, and responsible disclosure of discovered vulnerabilities. Professional certifications often include ethical standards codes, helping practitioners maintain integrity and avoid misuse of their skills.
Certification and Career Pathways in Ethical Hacking
For those interested in pursuing ethical hacking professionally, a variety of certifications can validate skills and enhance career prospects. The Certified Ethical Hacker (CEH) credential, offered by EC-Council, is one of the most recognized qualifications. Other certifications include Offensive Security Certified Professional (OSCP), CompTIA PenTest+, and GIAC Penetration Tester (GPEN). These certifications equip candidates with practical knowledge, test their capabilities, and establish their credibility in the cybersecurity landscape.
The Importance of Ethical Hacking for Organizations
Organizations rely on ethical hacking to safeguard digital assets and maintain regulatory compliance. Regular penetration testing identifies risks before attackers can exploit them, reducing the likelihood of costly data breaches and downtime. Ethical hacking also helps businesses improve security awareness among employees by revealing human vulnerabilities like susceptibility to phishing. In today’s threat environment, embedding ethical hacking into security strategies is not optional but essential for operational resilience.
Challenges Faced in Ethical Hacking
Despite its importance, ethical hacking presents unique challenges. Keeping pace with constantly evolving attack methods requires continuous learning and adaptability. Ethical hackers must balance thoroughness with minimizing system disruption during tests. Moreover, some organizations harbor mistrust toward hackers, even ethical ones, complicating collaboration. Navigating complex legal landscapes and handling sensitive data responsibly also add layers of complexity to the profession.
Future Trends in Ethical Hacking
As technology advances, ethical hacking evolves in tandem. Artificial intelligence and machine learning introduce new opportunities to automate vulnerability detection and analyze threats. Conversely, cybercriminals are leveraging these same technologies to launch more sophisticated attacks. Ethical hackers will increasingly integrate AI-based tools into their methodologies while focusing on emerging domains like Internet of Things (IoT) security, cloud infrastructure, and blockchain technologies. The future of ethical hacking lies in staying at the cutting edge of both offensive and defensive techniques.
Conclusion
Ethical hacking is a vital pillar of modern cybersecurity, empowering organizations and individuals to anticipate and mitigate digital risks proactively. Through a disciplined, legally authorized approach, ethical hackers uncover vulnerabilities before malicious actors can exploit them, effectively acting as guardians of the digital world. Mastery of technical skills, a strong ethical foundation, and continuous learning are essential for success in this dynamic field. As technology advances and cyber threats grow in complexity, the role of ethical hacking will only become more crucial. Embracing ethical hacking not only protects valuable data but also fosters trust and resilience, paving the way for a safer digital future for all
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
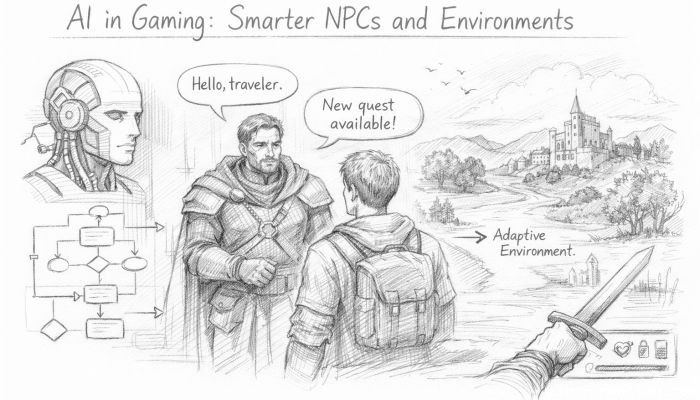 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
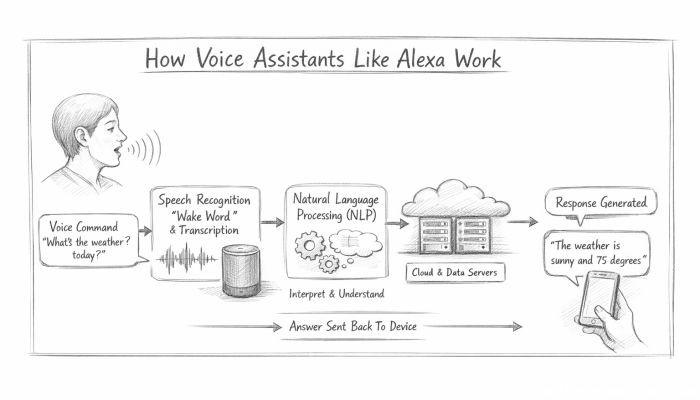 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data