How Ransomware Works
In today’s interconnected digital landscape, ransomware has emerged as one of the most pervasive and damaging cyber threats facing individuals, businesses, and governments alike. This malicious software locks victims out of their own data or systems, demanding a ransom payment—often in cryptocurrency—in exchange for restoration. As cybercriminals become increasingly sophisticated, understanding how ransomware functions is crucial not only for recognizing the risks but also for implementing effective defenses. This article delves deep into the mechanics of ransomware, breaking down its infection vectors, encryption mechanisms, ransom procedures, and methods for eviction. By dissecting each stage of a ransomware attack, we aim to provide a comprehensive overview of this complex cyber threat, equipping readers with insights that could help them better defend against or respond to an attack.
- What Is Ransomware?
- Initial Infection Vectors
- The Execution Phase
- File Encryption Mechanisms
- Targeted File Selection
- Displaying the Ransom Note
- Payment Methods and Cryptocurrency
- Communication With Attackers
- Evading Detection and Analysis
- Post-Infection Impact on Systems and Networks
- Prevention Strategies and Best Practices
- The Role of Law Enforcement and Cybersecurity Industry
- Conclusion
- More Related Topics
What Is Ransomware?
Ransomware is a type of malicious software (malware) designed to deny access to a computer system or data until a ransom is paid to the attacker. Unlike other forms of malware that might steal information or simply disrupt systems, ransomware specifically targets the victim’s ability to use their own files or devices. It achieves this by either encrypting files or locking the device. Since its rise in the mid-2000s, ransomware has evolved into a devastating threat, increasingly targeting corporate networks, government agencies, and critical infrastructure. Its success derives from the combination of high-impact disruption and the potential for lucrative payoffs, usually requested in untraceable cryptocurrencies like Bitcoin.
Initial Infection Vectors
Ransomware typically infiltrates systems through a range of attack vectors, each designed to exploit vulnerabilities in human behavior or software. The most common method is via phishing emails containing malicious attachments or links. Unsuspecting users open these attachments, triggering the download and execution of the ransomware payload. Other infection vectors include exploit kits that probe for software vulnerabilities on websites, malicious ads (malvertising), and software vulnerabilities—especially in remote desktop protocols (RDP) or outdated operating systems. Attackers also use direct manual hacks to deploy ransomware within high-value corporate or government environments, often after gaining initial access through stolen credentials.
The Execution Phase
Once ransomware enters a system, the execution phase begins. The malware runs its malicious code on the victim’s machine, often starting with checks for sandbox environments or antivirus tools to avoid detection. It then establishes persistence on the system, modifying registry entries or installing backdoors to survive reboots and maintain control. In some variants, ransomware will attempt lateral movement—spreading through network shares or exploiting trust relationships between machines—to increase the number of infected devices and maximize damage.

File Encryption Mechanisms
The core functionality of ransomware lies in its ability to encrypt files beyond the victim’s reach. It typically uses strong cryptographic algorithms such as AES (Advanced Encryption Standard) combined with asymmetric encryption like RSA. During the attack, the ransomware generates a unique encryption key, which is then used to scramble target files on the victim’s computer. Because the private key required to decrypt the files is held exclusively by the attacker, victims cannot regain access without payment (at least without sophisticated intervention or backups). This cryptographic process ensures that even if files are copied or moved, they remain inaccessible without the decryption key.
Targeted File Selection
Ransomware does not indiscriminately encrypt all files. It is often programmed to target specific file types considered most valuable to the victim. Common targets include documents (.docx, .pdf, .xls), images, databases, multimedia files, and backup data. This selective targeting ensures maximum disruption for the victim, increasing the likelihood that they will pay to regain access. Some ransomware variants also attempt to delete or encrypt shadow copies and backup files within the system to prevent recovery without paying the ransom.
Displaying the Ransom Note
After successfully encrypting data, ransomware displays a ransom note or warning message to the victim. This note usually contains instructions on how to pay the ransom and regain access. It may include threats such as data deletion after a deadline, the release of sensitive information, or increasing the ransom amount over time. The note often directs victims to Tor (The Onion Router) sites to facilitate anonymous communication with the attacker. The language in these notes is crafted both to intimidate victims and provide clear guidance on how to proceed, aiming to convert fear into compliance.
Payment Methods and Cryptocurrency
One of the principal challenges in tracking ransomware attacks is the method of ransom payment. Criminals almost exclusively demand payment in cryptocurrencies such as Bitcoin or Monero. These digital currencies provide a degree of anonymity and ease of transfer across international borders. The use of cryptocurrency wallets makes it difficult for law enforcement agencies to trace the flow of funds back to the perpetrators. Attackers often provide detailed instructions on how to obtain cryptocurrency to victims who are not already familiar with them, underlining the professionalism and sophistication of modern ransomware gangs.
Communication With Attackers
Ransomware operators typically provide a communication channel through which victims can negotiate for their data’s return. This is often done via encrypted messaging platforms or dark web portals. Some attacker groups even offer “customer support” to assist victims with payment processes, reinforcing the business-like nature of these cybercriminal operations. Negotiations may reduce the ransom amount or extend payment deadlines. However, paying does not guarantee file recovery since some attackers ignore victims once paid, or the decryption tool may fail due to technical issues.
Evading Detection and Analysis
Modern ransomware is built to evade detection by security software and forensic analysis. Techniques include code obfuscation, polymorphism (changing the malware code with each infection), and timing delays that avoid sandbox environments. Some variants include “kill-switches” that prevent activation under certain conditions or analyze system environments for anti-malware signatures. This evolutive behavior makes it increasingly difficult for cybersecurity teams to identify and shut down ransomware promptly, increasing its damage potential before being contained.
Post-Infection Impact on Systems and Networks
Beyond file encryption, ransomware often causes systemic damage. Network files and shared drives may be encrypted, delaying critical business operations. In cases of ransomware attacks on hospitals, utilities, or government agencies, downtime can affect essential public services. Some ransomware strains integrate with data exfiltration, stealing files before encryption—allowing attackers to threaten victims with public release if ransoms go unpaid, a technique known as double extortion. This multilayered impact amplifies pressure on victims to comply quickly.
Prevention Strategies and Best Practices
Understanding how ransomware works is only the first step toward prevention. Effective strategies include educating users on recognizing phishing emails and suspicious links, regularly updating software, and implementing multi-factor authentication to protect remote access points. Organizations should maintain secure, isolated backups that allow data restoration without capitulating to ransom demands. Network segmentation and endpoint protection tools can restrict ransomware spread, while active monitoring and rapid incident response plans reduce infection consequences.
The Role of Law Enforcement and Cybersecurity Industry
To combat ransomware’s rise, law enforcement agencies worldwide collaborate to identify and apprehend criminal groups behind attacks. Cybersecurity firms continuously analyze ransomware strains to develop decryption tools, share threat intelligence, and improve defense technologies. International initiatives focus on regulating cryptocurrencies and disrupting the financial channels underpinning ransomware economies. While ransomware will likely remain a persistent threat, coordinated responses improve resilience and shorten attack lifespans.
Conclusion
Ransomware represents a sophisticated and evolving cyber threat that leverages cryptography, social engineering, and digital anonymity to extort victims. Its workings—from infection vectors and encryption techniques to ransom demands—combine technical prowess with psychological manipulation, posing significant challenges to cybersecurity efforts. As ransomware actors grow bolder and more innovative, understanding how ransomware works becomes vital for developing effective defenses. The best protection lies in layered security protocols, continuous user education, robust backup policies, and proactive incident response. By demystifying ransomware’s operational anatomy, stakeholders can better anticipate attacks, minimize damage, and reduce the financial and operational toll inflicted by this dangerous form of cybercrime.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
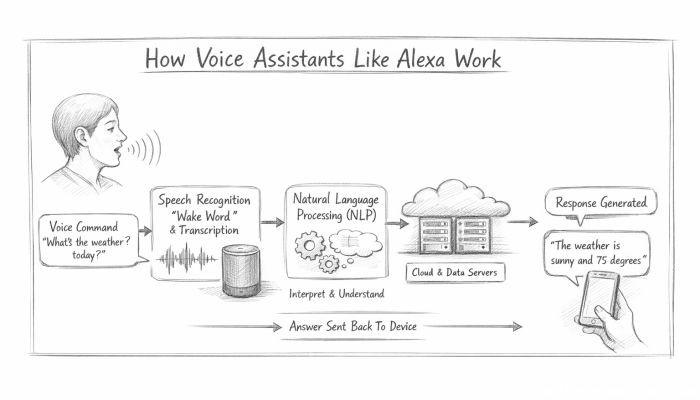 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data