Understanding Phishing Attacks
In today’s increasingly digital world, cybersecurity has become a paramount concern for individuals, businesses, and governments alike. Among the myriad of cyber threats that plague the internet, phishing attacks stand out as some of the most deceptive and damaging. Phishing is a form of cybercrime that lures unsuspecting victims into revealing sensitive information, such as passwords, credit card numbers, or personal identification details, often by masquerading as a trustworthy entity. As these attacks grow more sophisticated, understanding their mechanics, identifying warning signs, and learning preventive measures are essential steps in safeguarding one’s information. This article delves into the nature of phishing attacks, exploring their various forms, tactics, and the evolving landscape of cyber threats. Through a comprehensive examination, readers will gain both awareness and practical knowledge to defend against these malicious schemes.
- What is Phishing?
- Historical Background of Phishing
- Common Types of Phishing Attacks
- How Phishing Attacks Work
- Red Flags and Warning Signs of Phishing
- The Role of Social Engineering in Phishing
- Real-World Consequences of Phishing
- How Technology Helps (and Hinders) Fighting Phishing
- The Importance of Cybersecurity Awareness Training
- The Role of Multi-Factor Authentication (MFA)
- Emerging Trends: Phishing in the Era of Social Media and Mobile Devices
- Protecting Yourself and Your Organization from Phishing
- The Legal and Ethical Implications of Phishing
- Conclusion
- More Related Topics
What is Phishing?
Phishing is a cyberattack that involves fraudulently obtaining sensitive information by impersonating a trustworthy entity. Typically executed via email, phone calls, or text messages, phishing exploits human psychology more than technological weaknesses. Attackers create messages or websites that appear legitimate, convincing victims to click links, download malicious files, or enter confidential data. The term “phishing” originates from “fishing,” as attackers “fish” for valuable information by baiting unsuspecting recipients. While phishing often targets individuals, organizations large and small are common victims. The goal is to steal information, install malware, or gain unauthorized access to systems.

Historical Background of Phishing
Phishing attacks have evolved considerably over the past few decades. The first known phishing scams date back to the mid-1990s when attackers targeted America Online (AOL) users to steal passwords. At that time, attackers would impersonate AOL staff using simple chat messages to trick users. As internet usage expanded, so did phishing techniques. With the rise of email and social media, attackers developed more sophisticated and scalable methods. Today, phishing is a widespread problem, responsible for a significant portion of cybersecurity breaches globally. Understanding this history highlights how attackers have adapted to technological changes, emphasizing the need for continuous vigilance.
Common Types of Phishing Attacks
Phishing comes in various forms, adapting to different platforms and victim profiles. The most common types include:
- Email Phishing: The classic form, where fake emails impersonate reputable sources to trick recipients into clicking malicious links or sharing sensitive data.
- Spear Phishing: A highly targeted phishing attack aimed at specific individuals or organizations using personalized information to increase credibility.
- Whaling: A form of spear phishing targeting high-profile executives or decision-makers, often aiming for more significant financial or strategic gains.
- Smishing (SMS Phishing): Involves text messages that lure victims to malicious websites or prompt them to reveal personal information.
- Vishing (Voice Phishing): Attackers use phone calls or voicemail to impersonate trusted entities and extract confidential information.
Each type exploits different communication channels but shares the fundamental urge to deceive.
How Phishing Attacks Work
Phishing attacks are carefully designed to exploit human trust and curiosity. Typically, an attacker crafts a convincing message that may appear to come from banks, social media platforms, government agencies, or colleagues. The message often creates a sense of urgency—warning about suspicious account activity or promising a reward. This emotional manipulation compels victims to act quickly without verifying the source. Upon clicking a malicious link, victims might be redirected to a counterfeit website designed to look authentic. There, they enter login credentials or payment details, which the attacker records. Other times, attachments may contain malware that infects the victim’s device, enabling further exploitation.
Red Flags and Warning Signs of Phishing
Recognizing phishing attempts is the first line of defense. Common warning signs include:
- Suspicious Sender Address: Emails from unknown or misspelled domain names suggest fraud.
- Urgent or Threatening Language: Messages pressuring quick action without explanation.
- Generic Greetings: Use of "Dear Customer" instead of personalized names.
- Inconsistent Grammar or Spelling Errors: Professional organizations rarely send emails with blatant mistakes.
- Unsolicited Attachments or Links: Unexpected files or links demanding action.
- Requests for Sensitive Information: Legitimate institutions rarely ask for passwords or security details via email or text.
Being alert to these signs can prevent falling victim to phishing scams.
The Role of Social Engineering in Phishing
Phishing capitalizes on social engineering—the manipulation of people into performing actions or divulging confidential information. Attackers leverage psychological principles such as authority, reciprocity, fear, and urgency to manipulate victims. For example, a phishing email might claim to be from a bank’s security team, leveraging authority to compel the user to comply. Likewise, creating a fake urgent scenario or a supposed reward taps into emotions, clouding judgment. Because social engineering exploits human psychology rather than technical flaws, it’s challenging to defend against purely with technology. This underscores the critical importance of user education in any cybersecurity strategy.
Real-World Consequences of Phishing
The impact of phishing can be devastating for individuals and organizations alike. Victims may suffer financial losses through stolen bank details or fraudulent transactions. On a larger scale, phishing can lead to data breaches exposing sensitive customer or corporate information, damaging reputations and resulting in costly legal repercussions. In some cases, attackers use phishing to gain access to critical infrastructure or military systems, risking national security. For individuals, the personal impact ranges from identity theft to emotional distress. The widespread consequences highlight why phishing remains one of the most dangerous cybercrimes.
How Technology Helps (and Hinders) Fighting Phishing
Technology plays a dual role in the phishing landscape. On one hand, advancements such as spam filters, email authentication protocols (like SPF, DKIM, and DMARC), and AI-powered threat detection significantly reduce the quantity and success rate of phishing attacks. Browsers now warn users of suspicious websites, and two-factor authentication adds an extra layer of protection. However, technology can also aid attackers. Automated tools allow mass distribution of phishing messages, and deepfake technology can create convincing voice or video impersonations for vishing attacks. Moreover, the increasing use of encrypted communication channels can obscure phishing content from detection tools. Therefore, technology is both a powerful defense tool and a catalyst for more sophisticated attacks.
The Importance of Cybersecurity Awareness Training
Given the human-centric nature of phishing, education is key to prevention. Cybersecurity awareness training educates individuals and employees about recognizing phishing attempts, practicing safe browsing, managing passwords, and responding appropriately. Regular training sessions, simulated phishing tests, and up-to-date educational material build a security-conscious culture that reduces risk. For organizations, investing in employee awareness can prevent costly breaches. For individuals, staying informed helps avoid falling prey to scams that may cause personal or financial harm. Awareness training empowers users to be active participants in their own security rather than passive victims.
The Role of Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) strengthens security by requiring users to verify their identity through multiple proof points, such as passwords, biometric data, or temporary codes sent to devices. Even if attackers obtain login credentials via phishing, MFA can prevent unauthorized access without the second form of verification. This additional barrier dramatically reduces the success rate of phishing-based account takeovers. Although MFA is not foolproof and some advanced attacks attempt to bypass it, it remains one of the most effective security controls available. Encouraging or mandating MFA use is a critical step in securing personal and organizational accounts.
Emerging Trends: Phishing in the Era of Social Media and Mobile Devices
Phishing is no longer confined to email; attackers exploit social media platforms and mobile devices to reach victims. Social media phishing involves fake profiles, malicious links in direct messages, or posts impersonating friends and brands. Mobile devices, with their smaller screen sizes and limited display of URLs, make detecting phishing links more difficult, increasing vulnerability. Additionally, the rise of apps and third-party integrations creates new attack surfaces. Attackers also exploit mobile banking apps and SMS (smishing) to deceive users. The shift towards mobile and social media demands updated security approaches and continuous vigilance tailored to these platforms.
Protecting Yourself and Your Organization from Phishing
Protection against phishing requires a multifaceted approach. Start by adopting good digital hygiene: use strong, unique passwords managed through password managers, enable MFA, and keep software updated. Scrutinize suspicious emails and avoid clicking unknown links or opening unfamiliar attachments. Organizations should implement robust email filters, conduct regular training, and enforce security policies and access controls. Backing up critical data reduces impact in case of successful attacks. Reporting phishing attempts to relevant authorities or IT departments can help prevent wider harm. Finally, cultivating a cautious mindset toward unsolicited communications ensures long-term resilience against phishing threats.
The Legal and Ethical Implications of Phishing
Phishing is illegal under laws targeting cybercrime, data theft, and fraud in most countries. Perpetrators face criminal charges, fines, and imprisonment. Beyond legal consequences, phishing presents significant ethical concerns as it undermines trust, exploits vulnerabilities, and causes substantial harm. The proliferation of phishing also drives demand for stronger regulations around data protection, cybercrime enforcement, and corporate responsibility. Some countries now require organizations to disclose data breaches, incentivizing investments in defense. Ethical cybersecurity practices include promoting awareness, transparency, and responsible data management to combat the damaging effects of phishing.
Conclusion
Phishing attacks represent a persistent and evolving threat in the digital age, exploiting human psychology to gain unauthorized access to sensitive information. From their origins targeting AOL users in the 1990s to today’s sophisticated social media and mobile device scams, phishing poses a serious risk to individuals and organizations worldwide. Understanding the diverse methods attackers use, recognizing warning signs, and adopting layered defense strategies—such as cybersecurity awareness, multi-factor authentication, and robust technological measures—are critical to mitigating this threat. As phishing techniques continue to advance alongside new technologies, maintaining vigilance and continuous education remain paramount. By fostering a culture of security-conscious behavior and leveraging modern defenses, individuals and organizations can better protect themselves in an increasingly perilous cyber landscape
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
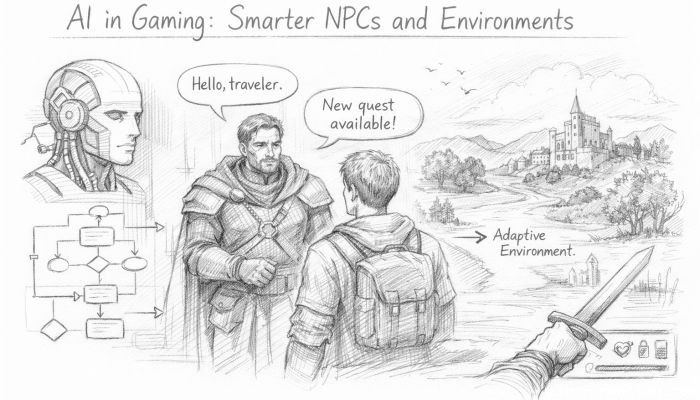 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
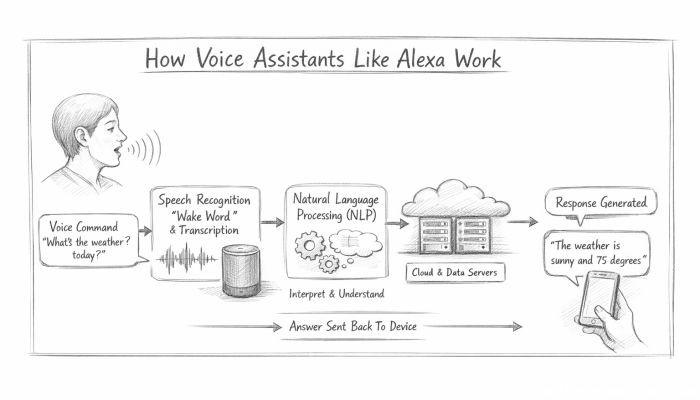 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data