The Role of Firewalls in Network Security
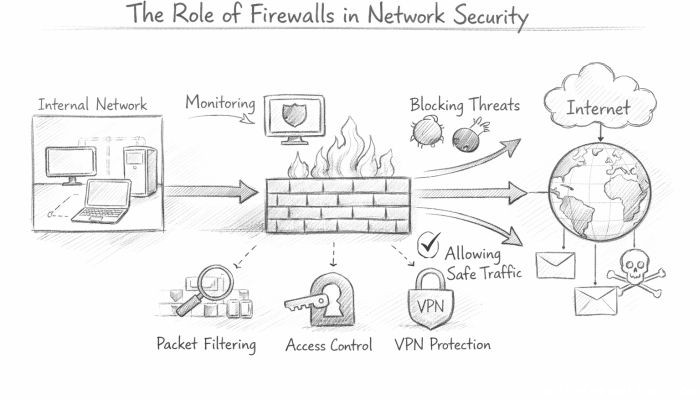
In today’s digital age, where information flows freely across the globe and cyber threats loom at every corner, maintaining robust network security has become paramount for individuals and organizations alike. Among various security tools and strategies, firewalls stand out as a critical first line of defense. Acting as gatekeepers, firewalls monitor, control, and filter incoming and outgoing network traffic based on predetermined security rules. By doing so, they help prevent unauthorized access, cyberattacks, and data breaches that could otherwise lead to significant financial losses, reputational damage, and compromised privacy. This article explores the vital role firewalls play in network security, detailing their functions, types, deployment methods, and challenges. By understanding how firewalls operate and their place in a comprehensive security strategy, readers can better appreciate their value in protecting digital assets in an increasingly interconnected world.
- What is a Firewall?
- Historical Evolution of Firewalls
- Types of Firewalls
- How Firewalls Enforce Security Policies
- Firewalls and Network Segmentation
- Role of Firewalls in Preventing Cyberattacks
- Firewall Deployment Strategies
- Challenges in Firewall Management
- Firewalls and Emerging Technologies
- Complementing Firewalls with Other Security Measures
- Future of Firewalls
- Best Practices for Effective Firewall Use
- Conclusion
- More Related Topics
What is a Firewall?
A firewall is a network security device or software that monitors and controls the flow of network traffic based on a set of defined rules established by system administrators. It acts as a barrier between trusted internal networks and potentially dangerous external networks like the internet. Firewalls can be hardware-based, software-based, or a combination of both, and they analyze data packets traversing the network to determine whether they should be allowed or blocked. The primary goal of a firewall is to prevent unauthorized access while permitting legitimate communications, thus safeguarding the confidentiality, integrity, and availability of data within a network.
Historical Evolution of Firewalls
The concept of firewalls dates back to the late 1980s as networks started to expand and the internet began gaining widespread use. Early firewalls were simple packet filters that operated at the network layer, inspecting packet headers to allow or deny traffic based on IP addresses and ports. Over time, as cyber threats became more sophisticated, firewalls evolved into stateful inspection devices that track active connections. Later advancements brought application layer filtering and deep packet inspection capabilities, enabling firewalls to scrutinize the content of data packets for more precise security enforcement. This evolution reflects the continually changing landscape of network threats and the necessity for firewalls to adapt accordingly.
Types of Firewalls
Firewalls come in various forms, each with distinct features and use cases. Packet-filtering firewalls examine packets at the network layer, allowing or blocking traffic based on IP addresses and ports. Stateful firewalls keep track of active connections and make decisions based on the state and context of network sessions. Proxy firewalls function at the application layer, acting as intermediaries between users and the internet, effectively hiding true IP addresses and filtering traffic more granularly. Next-Generation Firewalls (NGFWs) combine traditional firewall capabilities with features like intrusion prevention systems (IPS), deep packet inspection, and application awareness to handle modern threats. Selecting the right firewall depends on the specific needs and complexity of the network being protected.
How Firewalls Enforce Security Policies
Firewalls enforce security policies by defining and applying sets of rules known as access control lists (ACLs) that specify which types of traffic can pass through and which must be blocked. These rules can be based on IP addresses, ranges, ports, protocols, or even time of day. When a data packet arrives, the firewall examines it against these rules, determining if it complies with the predefined policies. If the packet matches an allow rule, it is forwarded to its destination; if it matches a deny rule, it is discarded. Effective firewall management requires constant updates and adjustments to these policies to respond to evolving security requirements and emerging threats.
Firewalls and Network Segmentation
Network segmentation involves dividing a larger network into smaller, isolated sub-networks to enhance security and performance. Firewalls play a crucial role in enforcing boundaries between segments, controlling the flow of traffic between different parts of the network. By segmenting networks and deploying internal firewalls, organizations can limit lateral movement by attackers who may have breached one segment, thereby containing potential damage and reducing risk. Moreover, segmentation helps enforce granular security policies tailored to different departments or systems, such as separating guest Wi-Fi access from sensitive corporate data zones.
Role of Firewalls in Preventing Cyberattacks
Firewalls are fundamental in defending against a wide array of cyberattacks, including unauthorized access attempts, malware distribution, and denial-of-service (DoS) attacks. By controlling inbound and outbound traffic, firewalls can block malicious packets or suspicious connections before they reach vulnerable systems. Advanced firewalls equipped with intrusion prevention capabilities can detect and respond to attack patterns in real-time. They also prevent unauthorized outbound communications, which is essential to stop data exfiltration or communication with attacker-controlled servers. In conjunction with other security tools, firewalls form an integral part of a multi-layered defense strategy.
Firewall Deployment Strategies
Deploying firewalls effectively requires strategic planning to maximize network security without hindering performance or usability. Firewalls are typically placed at key network junction points, such as the perimeter between the corporate network and the internet—a setup known as a perimeter firewall. Additionally, internal firewalls are often deployed between different network segments to protect sensitive areas. Organizations may use a “defense in depth” approach, layering multiple firewalls along with other security controls. In cloud environments, virtual firewalls are deployed to protect cloud resources. Proper placement, configuration, and regular monitoring are essential to ensure firewalls fulfill their protective role effectively.
Challenges in Firewall Management
While firewalls are vital to network security, managing them presents several challenges. Keeping firewall rules updated and consistent with organizational security policies requires ongoing effort and expertise. Misconfigured firewalls can create security gaps or inadvertently block legitimate traffic, causing operational issues. The increasing complexity of networks and the explosion of devices and applications add layers of difficulty in writing and maintaining effective firewall policies. Furthermore, sophisticated attackers may use encrypted communications or evasive techniques to bypass firewall defenses. Addressing these challenges requires skilled administrators, automated tools, and integration with broader security frameworks.
Firewalls and Emerging Technologies
The rise of cloud computing, the Internet of Things (IoT), and software-defined networking (SDN) has transformed traditional network architectures, impacting the role of firewalls. Cloud environments, for example, require virtual firewalls and integrated security services to protect dynamic and scalable resources. IoT devices, often lacking strong built-in security, increase the attack surface, making firewall visibility and control crucial. SDN enables more flexible and programmable firewall deployment, allowing security policies to be dynamically enforced and adapted. These emerging technologies necessitate evolving firewall capabilities and integration with advanced threat intelligence and analytics.
Complementing Firewalls with Other Security Measures
While firewalls are critical, they operate best as part of a comprehensive security ecosystem. Combining firewalls with antivirus software, intrusion detection and prevention systems (IDPS), security information and event management (SIEM) solutions, and endpoint protection strengthens defenses. Firewalls handle traffic control and access rules, but other tools can detect, analyze, and remediate threats that circumvent perimeter defenses. Additionally, employee training, security policies, and regular audits reinforce the human and procedural aspects of network security. This holistic approach is necessary to address the multi-faceted nature of modern cyber threats.
Future of Firewalls
Looking ahead, firewalls will continue evolving to meet the demands of increasingly complex and hostile threat environments. Artificial intelligence (AI) and machine learning (ML) technologies are being integrated into next-generation firewalls to improve threat detection by analyzing patterns and anomalies automatically. Zero-trust security models, which assume no implicit trust in any network component, require firewalls to enforce strict access controls continuously and contextually. The convergence of firewall functions with cloud security platforms and endpoint protection will become more pronounced, delivering unified security management. Despite changing technologies, firewalls will remain an indispensable cornerstone of network defense mechanisms.
Best Practices for Effective Firewall Use
To maximize firewall effectiveness, organizations should adhere to best practices encompassing policy development, configuration, monitoring, and maintenance. Defining clear, principle-based security policies aligned with organizational risk appetite is foundational. Regularly auditing firewall rules, removing unnecessary permissions, and minimizing rule complexity reduce vulnerabilities. Employing logging and monitoring tools to track firewall activity helps identify and respond to suspicious behavior promptly. Incorporating automation for routine tasks enhances efficiency and consistency. Finally, training IT staff on firewall management and keeping abreast of evolving risks ensures that the firewall remains a robust shield against cyber threats.
Conclusion
Firewalls are essential pillars of network security, serving as vigilant gatekeepers that regulate traffic and defend against unauthorized access, cyberattacks, and data breaches. From their humble beginnings as simple packet filters to today’s sophisticated next-generation devices, firewalls have adapted to an ever-evolving threat landscape. Their crucial roles include enforcing security policies, segmenting networks, preventing cyberattacks, and integrating with modern technologies such as cloud computing and IoT. However, maximizing firewall benefits requires careful deployment, continuous management, and integration with complementary security measures. As technology advances and cyber threats grow more complex, firewalls will continue to evolve, leveraging AI and zero-trust models to safeguard our digital futures. Understanding and effectively utilizing firewalls empowers organizations and individuals alike to build resilient defenses in an increasingly interconnected world.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
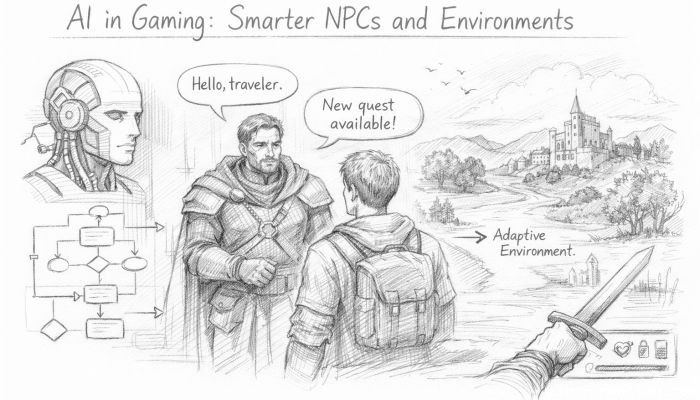 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
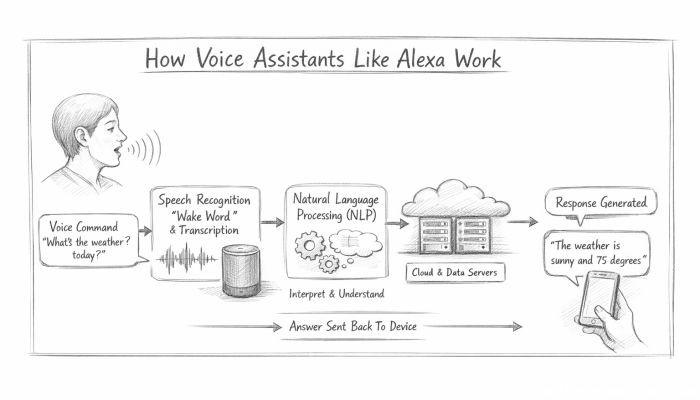 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data