How to Secure Financial Data in the Cloud
In the fast-paced digital world of today, and especially in our globalised economy, more and more sensitive data is stored, processed and accessed in cloud environments. Whether you’re working with your bookkeeping system, customer payment records, investment dashboards or treasury management, that financial data is a high‑value target for cyber‑attackers. At the same time, cloud platforms provide great flexibility, scalability and opportunity—but with it comes shared responsibility and new risk surfaces. In this article, we’ll walk through how to secure financial data in the cloud, step by step: covering governance and policy, encryption and identity, network and resource controls, monitoring and compliance, business continuity and more. The truth is: cloud security isn’t optional for financial data—it’s foundational to trust, efficiency and regulatory compliance.
- Understand the Shared Responsibility Model
- Classify and Inventory Your Financial Data
- Apply Robust Access Control and Identity Management
- Encrypt Data at Rest, in Transit and in Use
- Secure APIs and Integrations Handling Financial Data
- Implement Network‑and‑Cloud‑Resource Controls
- Establish Real‑Time Monitoring, Logging and Incident Response
- Backup, Disaster Recovery and Business Continuity Planning
- Maintain Compliance, Governance and Financial‑Sector Regulations
- Manage Third‑Party Risk, Vendor Access and Data Services
- Adopt a Culture of Security: Training, Awareness and Human Controls
- Review, Audit and Adapt Your Cloud Financial‑Data Strategy Regularly
- Conclusion
- More Related Topics
Understand the Shared Responsibility Model
The first step to securing financial data in the cloud is recognising that with cloud computing, security responsibilities are shared between the cloud service provider and the customer. According to Microsoft’s security blog, “the biggest problem is discovering where sensitive data is” and that the shared responsibility model means that the customer is in control of data, identity and access controls while the provider takes responsibility for the physical infrastructure and “generic components.” Microsoft+1 With financial data, this means a proactive approach in deliberately designing your policies, configurations and monitoring—instead of assuming the provider “does it all” by default. Understanding this shared responsibility is the foundation of all other cloud security controls.

Classify and Inventory Your Financial Data
Before you can protect financial data, you need to know where it is and how sensitive it is. Effective data classification means segmenting data into different tiers (public, internal, confidential, restricted) and applying stronger controls for restricted‑level data such as customer payment details or financial forecasts. nuharborsecurity.com+1 Inventorying your cloud assets—databases, storage buckets, logs, backups—is also critical. Use a data‑discovery tool to find “dark data” (unused, forgotten but still accessible). Once you know what you have, you can apply appropriate protection, retention and access rules.
Apply Robust Access Control and Identity Management
Financial data is highly sensitive and must be tightly controlled; access by over‑privileged users is a common risk vector. The principle of least privilege—granting only the access needed to do a job—is essential. nuharborsecurity.com+1 Use role‑based access control (RBAC) and attribute‑based controls to ensure that accounts don’t accumulate permissions over time (privilege creep). Identity and Access Management (IAM) must include multi‑factor authentication (MFA) so that stolen credentials aren’t enough to compromise accounts. Accounting for Everyone+1 Oversight and periodic review of permissions can help with reducing internal threats or accidental exposure.
Encrypt Data at Rest, in Transit and in Use
Encryption is non‑negotiable when it comes to protecting financial data in the cloud. According to best‑practice guides, you should encrypt both data at rest (stored data) and data in transit (in flight between services). Microsoft+1 Ideally you’d also encrypt while processing if feasible. Use strong encryption algorithms (AES‑256) and ensure that encryption keys are well managed, rotated, and access restricted. Many cloud providers offer key‑management services, but you may prefer Bring Your Own Key (BYOK) or Hardware Security Modules (HSMs) to keep full control of decryption. bobsguide.com Strong encryption protects the data itself even if storage or network controls are compromised.
Secure APIs and Integrations Handling Financial Data
Financial systems in the cloud often involve APIs that connect different internal systems, third‑party services, client apps and legacy infrastructure. These APIs become prime targets for attack. Best practices recommend strong authentication, encryption, rate limiting and monitoring for API endpoints. Microsoft+1 Ensure all financial‑data flows are authenticated, encrypted, and logged whether between microservices or with external vendors. You should also pen‑test and scan your APIs for vulnerabilities to guard against common API issues like injection, mis‑configuration or broken authorisation logic.
Implement Network‑and‑Cloud‑Resource Controls
Proper network segmentation and resource hardening can help contain breaches and reduce lateral movement in a cloud environment. According to cloud‑security guides, you should adopt a Zero Trust approach and not implicitly trust any entity, continuously verifying instead. CloudDefense.AI Use virtual private clouds, service‑endpoints, and firewalls or network security groups to isolate sensitive financial workloads from generic traffic. Monitor ingress and egress traffic, and ensure that cloud resources such as databases or storage buckets are not inadvertently exposed to public networks. Regular patching and lifecycle management of virtual machines and containers are also essential. Accounting for Everyone
Establish Real‑Time Monitoring, Logging and Incident Response
Even with the best prevention controls, you cannot prevent all events. Ongoing monitoring, log‑collection and anomaly detection are key to detecting compromise early and limiting the damage. Best‑practice resources emphasise the need for continuous auditing of cloud activity: access logs, configuration changes, data exports and API usage. Netwoven+1 Use SIEM (Security Information and Event Management) or cloud‑native equivalents to centralise alerts and trigger incident response. Have an incident‑response plan specific to cloud‑based financial data breaches—define roles, escalation paths, data‑breach notification procedures and recovery workflows. Preparedness turns a breach into a managed event.
Backup, Disaster Recovery and Business Continuity Planning
Financial data needs to be available, accurate and protected even in disruptive events—whether malware, system failure or human error. Backup and disaster‑recovery planning is a part of your cloud‑financial‑data strategy. NetWize+1 Backup your cloud‑data securely (encrypted, geographically separated, immutable snapshots if possible), test your restore procedures regularly, and consider ransomware scenarios (e.g., crypto‑shredding or key compromise). In the event of a breach affecting data integrity or availability, your ability to recover quickly without major loss of finance‑data integrity is crucial for trust and regulatory compliance.
Maintain Compliance, Governance and Financial‑Sector Regulations
Financial‑data protection is not just good practice, it’s often required by regulation. Whether you’re subject to PCI‑DSS (payments data), GDPR (personal data), SOX (public companies) or sector‑specific rules (FINRA, Basel, etc.) you must demonstrate controls, audit trails and breach notification readiness. Best‑practice articles emphasise that encryption, logging, controlled access and vendor‑management are foundational to compliance. bobsguide.com Document your policies, review vendor contracts regularly and maintain evidence of security controls. Weak cloud governance can lead to major financial and reputational penalties—especially in the finance sector.
Manage Third‑Party Risk, Vendor Access and Data Services
In a cloud ecosystem, your organisation often relies on SaaS, PaaS or IaaS providers—and each introduces risk. According to experts, you should assess vendor controls, contract responsibilities, security certifications (e.g. ISO 27001, SOC2) and access privileges. Reddit Enforce vendor‑access policies and segmentation to ensure that third‑party services cannot inadvertently compromise your financial‑data environment. Regularly review which vendors have access, audit their logs and ensure third‑party agreements include cloud‑security expectations consistent with your own. This reduces the potential for supply‑chain compromise.
Adopt a Culture of Security: Training, Awareness and Human Controls
Technology alone cannot protect financial data in the cloud. Humans remain a key risk factor, whether through phishing, mis‑configuration or accidental sharing. Security guidance emphasises training employees on secure behaviour: strong password hygiene, scam awareness, access rights management, and understanding cloud‑config risks. Salesforce Promote a culture where data classifications are respected, permissions removed when staff change roles and regular drills test the incident‑response team. When your team knows how to act and handle financial data with caution, your technical controls become far more effective.
Review, Audit and Adapt Your Cloud Financial‑Data Strategy Regularly
Cloud environments and usage change rapidly: new services are provisioned, usage patterns shift, and threats emerge and adapt. To maintain secure financial‑data protection, you must conduct periodic reviews. Regular audits—permissions, encryption‑key management, data flows, vendor access, policy adherence—ensure you stay current. Best‑practice sources note that regular assessment (pen testing, config reviews, third‑party audits) is essential. Netwoven+1 As your business grows and usage scales, ensure your cloud architecture, governance and financial‑data controls scale too. Security is not set‑and‑forget, it’s dynamic.
Conclusion
Securing financial data in the cloud is a mission‑critical undertaking—not a checkbox. From understanding the shared responsibility model to data classification, implementing strong identity controls, encryption, network segmentation, monitoring, incident response and disaster‑recovery plans; from vendor governance to compliance frameworks, human training and continuous review—each layer builds resilience. In the finance sector, where trust and integrity are cornerstones, cloud‑data breaches can have both financial and reputational impacts. Yet with methodical planning and execution, cloud platforms can provide flexibility, scalability and strong security. Build your controls, test your workflows and treat security as a continuous, adaptive process. When you do it right, you’re not just protecting data, you’re safeguarding financial stability and business resilience.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
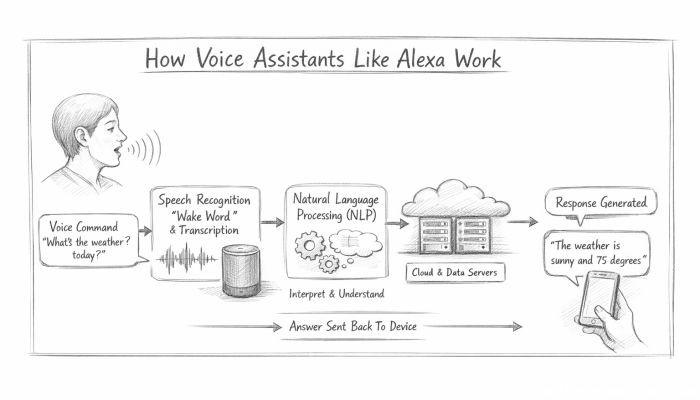 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data