How to Secure Your Crypto Wallet
Welcome to the future of finance! As cryptocurrency adoption soars globally, we’ve seen the rise of a new financial era dominated by digital assets. From Bitcoin (BTC) to Ethereum (ETH), stablecoins to NFTs, the crypto world is exploding with opportunities for investors, traders, and enthusiasts alike. But while these innovations are undoubtedly exciting, there’s one thing that comes with crypto that the traditional banking system doesn’t: non-stop security threats. Wallet hacking, phishing scams, exchange breaches, and rug pulls — the crypto universe is a constant battle against hackers and scammers. But don’t worry — the good news is that most of these threats are easily avoidable with a few simple precautions. At its core, securing your crypto wallet is easy. Choose a reputable wallet, use strong passwords and 2FA, keep your software updated, and most importantly, be aware of the risks. By following this guide, you’ll be able to enter the crypto realm with confidence, without fear of getting hacked or losing your funds. And who knows — with the right knowledge, you might even come out ahead, becoming a crypto tycoon along the way! So let’s get started and secure those digital assets.
- Understand Why Wallet Security Matters
- Choose the Right Type of Crypto Wallet
- Keep Your Private Keys Safe
- Secure Your Recovery Phrase
- Use a Hardware Wallet for Optimal Security
- Implement Two-Factor Authentication (2FA)
- Avoid Phishing and Scams
- Keep Your Software Updated
- Use a Secure Internet Connection
- Diversify Your Wallets and Assets
- Practice Physical and Environmental Security
- Plan for the Future: Estate and Backup Management
- Conclusion
- More Related Topics
Understand Why Wallet Security Matters
First, let’s understand why wallet security is so important. Your crypto wallet is your access point to the decentralized world of digital assets. It’s where your private keys live, the passwords that allow you to access your cryptocurrencies on the blockchain. Wallets can take many forms, such as hardware, software, mobile, desktop, or web-based, but they all have one common purpose: to securely store your private keys so you can use them to sign transactions — from sending a few satoshis to someone as a gift to exchanging thousands of dollars’ worth of ETH or buying your first NFT.

There’s no centralized authority for crypto like there is with fiat money in banks. If your keys are stolen or lost, no one can restore them for you. The blockchain is immutable and final — once a transaction has been made, it can’t be reversed. So if you lose your private keys, it’s game over for your crypto funds.
That’s why having a strong and secure wallet is critical for every crypto investor, trader, or enthusiast. Wallet security also goes beyond simple protection against loss or theft. In the current crypto ecosystem, your wallet is also your gateway to DeFi, decentralized exchanges (DEXs), staking platforms, lending, and more. As you move into the greater DeFi ecosystem, the need for strong wallet security becomes even more crucial. By following best practices and being diligent about your crypto security, you’ll be able to fully enjoy the crypto experience without the fear of getting hacked or losing your hard-earned crypto.
Choose the Right Type of Crypto Wallet
Wallets come in various types, each with unique features and levels of security. Before you choose one, it’s important to understand the differences.
Hot wallets are connected to the internet and include mobile wallets, desktop wallets, and web wallets. They’re convenient for frequent transactions, trading, or staking but more vulnerable to online threats.
Cold wallets, on the other hand, store your crypto offline and include hardware wallets and paper wallets. Hardware wallets are physical devices that hold your private keys offline for maximum security, while paper wallets are printouts of your private keys and addresses stored offline. Cold wallets are less convenient for active traders but are considered much more secure, especially against online hacking attempts.
The right wallet for you depends on your needs. Active traders and stakers may prefer hot wallets for ease of use, while long-term investors may opt for the higher security of a cold wallet. Many crypto enthusiasts use a combination of both — a hot wallet for smaller, everyday funds and a cold wallet for long-term investments. Choose a reputable wallet with a proven track record in the crypto community, such as Ledger or Trezor for hardware wallets, MetaMask or Trust Wallet for mobile wallets, and Coinomi or Exodus for desktop wallets. Whichever wallet you choose, it should be user-friendly, secure, and compatible with your preferred cryptocurrencies and DeFi platforms.
Keep Your Private Keys Safe
Your private keys are the most important aspect of your wallet’s security. They are like passwords to your crypto, and whoever has them can access your funds. Never share your private keys with anyone or store them in an unencrypted digital location like an email, cloud storage, or note app. The best practice is to write them down on a piece of paper and keep them in a secure location, like a safe, fireproof, and waterproof. You can also use a hardware device for long-term safekeeping of your private keys.
Some investors go as far as splitting their private keys across multiple secure locations so that if one is compromised, the others remain safe. If your private keys are lost, stolen, or destroyed, you will lose access to your crypto funds permanently, so it’s essential to take extra care of them and keep them safe at all times.
Secure Your Recovery Phrase
Most crypto wallets provide you with a recovery phrase, also known as a seed phrase, which is a series of 12 to 24 words that can be used to restore your wallet if your device is lost, damaged, or inaccessible. Your recovery phrase has master access to your wallet, so it’s important to keep it safe and secure at all times. Never take a screenshot of your recovery phrase or store it in any digital format, including cloud storage or note apps. Instead, write it down on paper or use a metal backup plate that can withstand fire and water damage. Store multiple copies of your recovery phrase in multiple secure locations, like a home safe or safety deposit box. You should never share your recovery phrase with anyone or enter it into any website other than your original wallet. Scammers often create fake wallet interfaces to trick users into entering their recovery phrases, which they then use to steal the user’s funds instantly.
Use a Hardware Wallet for Optimal Security
Hardware wallets are widely considered the safest option for long-term investors. These physical devices store your private keys offline, away from the potentially compromised online environment. When you use a hardware wallet to sign a transaction, the device internally signs it and only sends the approved transaction data to your connected device, keeping your private key safe and secure. Hardware wallets can be an upfront investment, but they offer the highest level of protection against malware, phishing scams, and exchange hacks.
When buying a hardware wallet, make sure you purchase it directly from the manufacturer’s website to avoid any counterfeit products. Ledger Nano X and Trezor Model T are two of the most popular hardware wallets in the industry, known for their strong security and user-friendly features.
Implement Two-Factor Authentication (2FA)
Two-factor authentication (2FA) adds an extra layer of security to your wallet and exchange accounts, ensuring that even if someone obtains your password, they won’t be able to access your account without the second verification step. You can usually find 2FA settings in the security section of your wallet or exchange account.
Avoid SMS-based 2FA since SIM-swapping attacks can intercept text messages. Instead, use an authenticator app such as Google Authenticator, Authy, or Microsoft Authenticator for generating your 2FA codes. For the most security-conscious, you can even use a hardware security key like YubiKey, which requires physical interaction for verification. Think of 2FA as a digital safety net that can catch even the most sophisticated hacking attempts.
Avoid Phishing and Scams
Phishing remains one of the most prevalent and successful hacking techniques against cryptocurrency users. Scammers create fake websites, apps, or emails that mimic the look and feel of legitimate platforms to trick users into entering their login credentials or recovery phrases. Always double-check URLs, bookmark websites, and never click on suspicious links. If you receive an email or message urging you to “act now” or claiming that your account is at risk or offering free crypto, be highly skeptical. Official support will never ask you for your private keys or seed phrases. If you have any doubts or concerns, visit the official website or community channels to verify before responding. Be aware of phishing scams and always stay vigilant against digital trickery.
Keep Your Software Updated
Cyber attackers are constantly finding new vulnerabilities in outdated software to exploit and gain unauthorized access to your wallet or exchange account. Regularly updating your wallet, operating system, and antivirus software is one of the simplest ways to prevent this. Enable automatic updates wherever possible and only download wallet software from official sources. For mobile wallets, only install apps from trusted app stores like Google Play or the Apple App Store. Browser-based wallets like MetaMask should only be used on secure browsers with no malicious extensions installed. By keeping your software up to date, you close potential security gaps that attackers could exploit and give your wallet’s overall defenses a much-needed boost.
Use a Secure Internet Connection
The internet connection you use to access your wallet or exchange account could be an easy target for hackers. Always use a secure, private network for accessing your crypto assets — never a public Wi-Fi network. Public networks are hotbeds for “man-in-the-middle” attacks where hackers intercept and manipulate your data. If you must connect remotely, use a Virtual Private Network (VPN) to encrypt your connection and mask your IP address. Do not share your device or login credentials with anyone, and avoid accessing your wallet or exchange accounts from shared or public computers. Your crypto access points should be as private and secure as a digital vault.
Diversify Your Wallets and Assets
Don’t put all your eggs in one basket. Avoid storing all your crypto in one wallet or exchange account. Diversifying your wallets reduces the risk of losing all your funds if one wallet is hacked. For example, you can have one wallet for small, everyday transactions, one for DeFi activities, and one cold wallet for long-term investments. Similarly, avoid using a single exchange for storage. Centralized platforms are often the target of large-scale hacks and attacks. By spreading your risk across multiple wallets and exchanges, you can mitigate the damage of a potential breach, which is a fundamental principle of smart crypto management.
Practice Physical and Environmental Security
Physical security can be just as important as digital security when it comes to protecting your crypto. If you keep your private keys, recovery phrases, or hardware wallets at home, ensure they are safe from theft, fire, and water damage. Use safes, lockboxes, or hidden storage areas, and avoid discussing your crypto holdings or revealing your wallet balances in public or on social media — this makes you a target. If your crypto holdings are significant, consider using a safety deposit box at a bank or a multi-signature wallet that requires multiple approvals for transactions. Think about physical redundancies as well as digital ones to protect against all forms of loss or destruction.
Plan for the Future: Estate and Backup Management
Crypto assets can outlive their owners, so it’s crucial to plan for their recovery or inheritance. Create a secure and clear record of how your heirs or trusted contacts can access your wallet in case of your incapacity or death without compromising your security during your lifetime. You can store instructions in a sealed letter, an encrypted digital file, or a legal document administered by a trusted executor. In addition to creating an inheritance plan, it’s also good practice to keep multiple backups of your wallet information, including private keys and recovery phrases, in different, geographically separate locations. Your crypto security plan should consider not only current risks but also future accessibility for you, your heirs, and other trusted parties.
Conclusion
Securing your crypto wallet is more than a technical checklist — it’s an act of financial empowerment. In the decentralized world of digital assets, you are your own bank, your own custodian, and your own security agent. The actions you take today will determine whether your digital wealth is protected or put on display for the world to see. From securing your private keys and using hardware wallets to enabling two-factor authentication and avoiding phishing scams, each small step builds upon the next to create an effective fortress that can withstand the rapidly evolving threat landscape. Remember, crypto security is not a set-it-and-forget-it job. It’s an ongoing process of staying informed, adapting, and implementing best practices. With due diligence, a healthy dose of skepticism, and the right knowledge, you can safely explore the crypto space without fear of hacking or loss.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
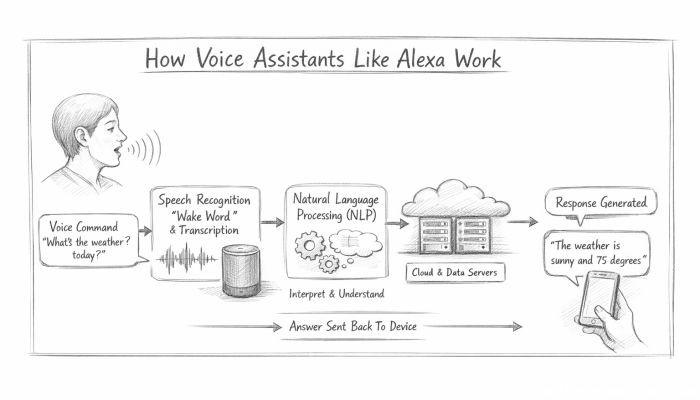 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data