How to Avoid Mobile App Scams
In an age where smartphones have become extensions of ourselves, mobile apps have revolutionized the way we communicate, shop, work, and entertain ourselves. However, this surge in app usage has also opened the floodgates for mobile app scams, exposing users to increasingly sophisticated frauds that threaten both privacy and finances. From fake apps impersonating trusted brands to malicious software designed to steal data, mobile app scams have become a growing hazard in the digital landscape. Understanding how to identify and avoid these scams is essential for safeguarding your personal information and enjoying a secure mobile experience. This article delves deep into practical strategies and insightful tips to help you navigate the app ecosystem confidently, shielding yourself from potential threats lurking in app stores and beyond.
- Understanding Mobile App Scams: An Overview
- Common Types of Mobile App Scams
- The Importance of Official App Stores
- Reading App Reviews and Ratings
- Scrutinizing App Permissions
- Checking Developer Credibility
- Utilizing Mobile Security Software
- Keeping Your Mobile Operating System Updated
- Avoiding Public or Unsecured Wi-Fi Networks
- Exercising Caution with App Links and Promotions
- Reading Privacy Policies Carefully
- Using Two-Factor Authentication (2FA)
- Reporting Suspicious Apps and Activities
- Conclusion: Staying Vigilant in a Digital World
- More Related Topics
Understanding Mobile App Scams: An Overview
Mobile app scams are deceptive programs masquerading as legitimate applications to exploit unsuspecting users. These scams range from phishing apps that steal login credentials, clones of popular apps designed to collect financial data, to malware-infused apps that hijack devices. The financial and personal risks associated with these scams are significant, often resulting in identity theft, financial loss, or unauthorized access to sensitive data. Recognizing the various forms these scams take is the first step toward developing a defensive stance in your mobile usage habits.

Common Types of Mobile App Scams
Among the myriad of mobile app frauds, some scams are more prevalent than others. Fake apps, which copy the name, logo, and functionality of well-known applications, attempt to trick users into downloading them. Another popular scam involves subscription traps, where free apps lure users in but quietly charge exorbitant fees in the background. There are also phishing apps disguised as legitimate login portals designed to harvest usernames and passwords. Additionally, spyware and ransomware apps covertly install malware that can compromise your device’s security. Awareness of these common types is critical to spotting red flags early on.
The Importance of Official App Stores
Official app stores like Google Play Store and Apple’s App Store enforce strict validation and security checks on the apps they list. While no store is immune to scams completely, downloading apps from these trusted platforms significantly reduces risks. Third-party app stores or downloading apps from unknown websites expose users to a higher likelihood of encountering fraudulent or malicious software. Therefore, always prioritize official sources when installing new apps to ensure you have the baseline of security protocols some of the most reputable platforms enforce.
Reading App Reviews and Ratings
One of the most effective tools users have to assess an app’s credibility is its user reviews and ratings in the app store. Genuine apps tend to accumulate hundreds or thousands of reviews, with balanced feedback highlighting both pros and cons. Conversely, scam apps often feature very few reviews, many of which may feel generic, overly positive, or suspiciously similar due to fake reviews generated to mislead. Look for detailed, authentic experiences rather than exclusively glowing or negative ones, and be cautious if an app lacks sufficient feedback or the reviews seem unnatural.
Scrutinizing App Permissions
Every app requests access permissions to certain functionalities on your device, such as the camera, contacts, or location services. However, excessive or unnecessary permission requests often indicate a potential scam or malicious intent. For example, a simple flashlight app that requires access to your contacts or microphone is a cause for concern. Studying the permissions an app requests and questioning their relevance to the app's advertised functionality can prevent you from unintentionally granting access to your private information.
Checking Developer Credibility
The developer’s identity and credibility are important markers of app legitimacy. Well-known developers or those with a substantial app portfolio tend to be more trustworthy. Official accounts often include clear contact information, websites, and regular updates. Conversely, apps published by anonymous developers or those with inconsistent names may signal scams. Performing a quick background check on the developer via online searches or visiting their official website can provide valuable context about their reputation and authenticity.
Utilizing Mobile Security Software
Installing and maintaining reputable mobile security or antivirus software adds an extra layer of defense against app scams. These tools can scan apps for malicious code, detect phishing attempts, and alert you about risky permissions or unusual app behavior. Many security suites also offer real-time protection and vulnerability assessments that help identify threats before they compromise your device. While not foolproof, leveraging such software significantly mitigates your exposure to mobile fraud.
Keeping Your Mobile Operating System Updated
Mobile operating system developers frequently release updates that patch security loopholes and enhance device protection. Keeping your phone’s OS updated ensures you benefit from the latest security enhancements, which scammers are less likely to circumvent. Delaying or ignoring system updates increases vulnerability to attack vectors exploited by malicious apps. Make it a habit to check for and install OS updates promptly as part of your security routine.
Avoiding Public or Unsecured Wi-Fi Networks
Mobile app scams often exploit unprotected public Wi-Fi networks to intercept data or inject malware. Using open Wi-Fi hotspots without a secure connection exposes your device, especially during app interactions involving sensitive or financial information. Whenever possible, avoid completing login or payment processes on public networks, or use a trusted Virtual Private Network (VPN) that encrypts your data traffic for safer transmission. This practice reduces the risk of falling prey to man-in-the-middle attacks frequently deployed in app scams.
Exercising Caution with App Links and Promotions
Scammers often lure users through fraudulent app links sent via emails, messages, or social media, enticing them with enticing offers or urgent warnings. Clicking on such links can lead to fake app downloads or phishing pages designed to capture credentials. Always verify the legitimacy of app promotions before installing and never download apps from unsolicited messages. If an app promotion seems too good to be true or pressures quick action, pause and investigate before proceeding.
Reading Privacy Policies Carefully
Privacy policies, though lengthy and often overlooked, contain crucial information about how an app collects, uses, and shares your data. Scam apps may have vague or nonexistent privacy policies, or include clauses that permit extensive data exploitation. Reviewing these policies helps you understand the potential risks and whether your data is handled responsibly. Trusted developers typically present clear, transparent policies reflecting compliance with data protection standards.
Using Two-Factor Authentication (2FA)
Wherever possible, enable two-factor authentication for apps and services linked to your mobile device. 2FA provides an additional security barrier by requiring a second form of verification, such as a code sent to your phone, alongside your password. This significantly reduces the impact of credential theft via fraudulent apps because an attacker cannot access your account with just the stolen login information.
Reporting Suspicious Apps and Activities
Actively reporting suspicious apps to app stores or security authorities contributes to broader user protection. Developers and stores can investigate and remove fraudulent applications more quickly when users flag malicious behavior. Additionally, reporting helps raise awareness and creates publicly available information that can prevent others from falling victim. While individual vigilance is crucial, collective action strengthens the app ecosystem’s safety net.
Conclusion: Staying Vigilant in a Digital World
Mobile app scams are a persistent and evolving threat in today’s interconnected world, where convenience meets complexity. Avoiding these scams demands a combination of informed skepticism, proactive habits, and leveraging security tools. By downloading apps only from official stores, scrutinizing permissions, verifying developer credibility, and employing protective measures such as security software and 2FA, you dramatically reduce your risk of becoming a victim. Staying alert to suspicious promotions and safeguarding your device with regular updates and network caution completes a solid defense strategy. Ultimately, your cybersecurity is in your hands—knowledge and vigilance are your best allies against mobile app scams, empowering you to enjoy the full benefits of mobile technology safely and securely.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
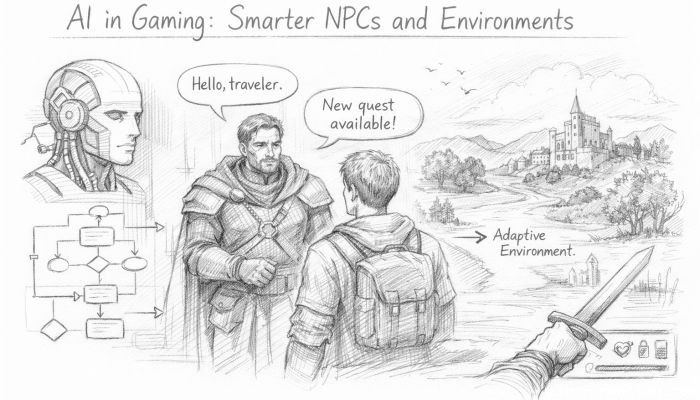 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
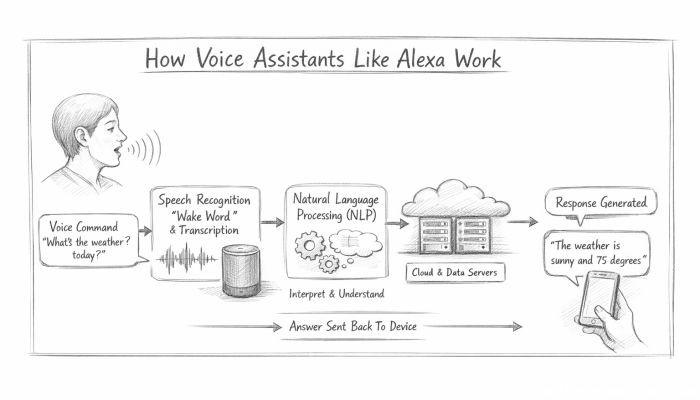 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data