Understanding DDoS Attacks
In today’s hyper-connected world, the availability and reliability of online services play a pivotal role in both personal and professional spheres. Yet, the increasing reliance on digital infrastructure also exposes individuals, businesses, and governments to sophisticated cyber threats. Among these threats, Distributed Denial of Service (DDoS) attacks stand out as one of the most prevalent and disruptive forms of cyber assault. DDoS attacks aim to overwhelm targeted systems, rendering websites, servers, or networks inaccessible for legitimate users. Understanding the technical intricacies, motivations behind these attacks, and the strategies to mitigate them is critical to safeguarding digital assets. This article delves deeply into the nature of DDoS attacks, their evolution, execution methods, impact, and defense mechanisms, providing readers with comprehensive insights into this complex threat landscape.
- What is a DDoS Attack?
- Historical Evolution of DDoS Attacks
- Types of DDoS Attacks
- Botnets: The Engines of DDoS Attacks
- The Motivations Behind DDoS Attacks
- How DDoS Attacks are Executed
- Impact of DDoS Attacks on Businesses
- Detection Techniques for DDoS Attacks
- Common Mitigation Strategies
- The Role of Cloud and CDN Providers in DDoS Defense
- Legal and Ethical Considerations Surrounding DDoS
- Preparing for the Future: Emerging Trends in DDoS Attacks and Defense
- Conclusion
- More Related Topics
What is a DDoS Attack?
A Distributed Denial of Service (DDoS) attack is a cyberattack where multiple compromised computers, often part of a botnet, flood a targeted system with overwhelming traffic to exhaust its resources. Unlike a traditional Denial of Service (DoS) attack, which usually originates from a single device, a DDoS attack leverages many devices distributed across the globe. This distributed nature makes it difficult to block the malicious traffic due to its sheer volume and diverse sources. The main objective is to disrupt the normal functioning of an online service, network, or server, making it unavailable to intended users and causing downtime and financial loss.

Historical Evolution of DDoS Attacks
DDoS attacks have evolved significantly over the past two decades. In the late 1990s and early 2000s, attackers primarily used simple flooding methods, such as ICMP (ping) floods, to disrupt services. One of the earliest large-scale incidents was the 2000 attack on Yahoo!, which slowed the site considerably. As technology advanced, attackers developed more sophisticated tools, such as botnets comprising hundreds of thousands of infected devices, including IoT devices. Milestones such as the Mirai botnet in 2016 underscored the threat posed by unsecured Internet-connected gadgets capable of launching massive DDoS attacks. This evolution reflects the increasing complexity and scale of these cyber threats over time.
Types of DDoS Attacks
DDoS attacks can be broadly categorized into three types: volumetric attacks, protocol attacks, and application layer attacks.
- Volumetric attacks inundate the bandwidth of a target site with an enormous amount of traffic, measured in packets per second (pps) or bits per second (bps). Examples include UDP floods and DNS amplification attacks.
- Protocol attacks exploit weaknesses in network protocols to consume server resources, causing degradation or failure. SYN floods and Ping of Death attacks fall in this category.
- Application layer attacks focus on specific web applications by sending seemingly legitimate but resource-intensive requests that exhaust server capacity. Examples include HTTP GET/POST floods.
Understanding these types helps defenders tailor specific countermeasures.
Botnets: The Engines of DDoS Attacks
At the heart of most DDoS attacks are botnets — networks of infected computers or devices under the attacker’s control. Botnets are created by distributing malware that allows attackers to commandeer a device without the owner’s knowledge. With the rise of IoT devices lacking robust security measures, botnets have grown exponentially, sometimes comprising millions of devices. Examples like the Mirai botnet turned everyday household items such as cameras and DVRs into attack vectors, amplifying the power and reach of DDoS campaigns. The decentralized structure of botnets complicates tracing and blocking efforts, making them formidable tools for attackers.
The Motivations Behind DDoS Attacks
Not all DDoS attacks are motivated by financial gain; their reasons vary widely. Some attackers seek political or ideological statements, referred to as hacktivism, targeting entities whose actions they oppose. Others use DDoS attacks as smokescreens to distract IT teams while breaching networks or stealing data. Financial extortion through ransom DDoS attacks is common, where attackers threaten prolonged service disruption unless a ransom is paid. Additionally, competitors might deploy DDoS attacks to disrupt rival businesses, while some attacks are launched for mere notoriety or testing offensive cyber capabilities. Understanding motivation aids in anticipating and preparing for potential threats.
How DDoS Attacks are Executed
Execution typically begins with assembling a botnet, followed by instructing the compromised devices to launch coordinated traffic towards a selected target. Attackers choose specific techniques based on their goals and the vulnerabilities of the target. For instance, they may use amplification attacks, which reflect and multiply traffic volumes by abusing protocols like NTP or DNS, sending large responses to the victim's IP address. Attackers also often employ multi-vector attacks that combine volumetric floods with application-layer requests to circumvent simple filtering methods. Sophisticated attackers may rotate attack patterns or use “low and slow” techniques to remain under detection thresholds while still degrading service.
Impact of DDoS Attacks on Businesses
The damage caused by DDoS attacks extends beyond immediate downtime. Financial losses due to disrupted sales, missed transactions, and remediation expenses can be severe. Brand reputation may also suffer when customers encounter service outages, leading to decreased trust and future revenue declines. Additionally, internal employee productivity may taper off during an incident as IT teams devote time to response and recovery. For certain industries like finance and e-commerce, even minutes of outage can translate into significant losses. Regulatory consequences might follow if service disruptions compromise data integrity or breach compliance standards, amplifying legal risks.
Detection Techniques for DDoS Attacks
Early detection is crucial to mitigating the effects of DDoS attacks. Various methods exist, ranging from traffic anomaly detection to signature-based identification. Network administrators employ Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) to monitor traffic patterns and flag abnormal surges or suspicious sources. Machine learning and artificial intelligence, increasingly integrated into security platforms, analyze vast amounts of data to detect subtle changes that might precede an attack. Behavioral analysis also helps distinguish malicious traffic from legitimate spikes in usage due to marketing campaigns or flash sales, thus reducing false positives and improving response accuracies.
Common Mitigation Strategies
Mitigating a DDoS attack involves multiple layers of defense. Rate limiting restricts the number of requests a user or IP address can make over a period, reducing the risk of flooding. Web Application Firewalls (WAFs) can filter out malicious application-layer traffic. Traffic scrubbing services, often offered by cloud providers, reroute traffic through cleaning centers that remove malicious packets, allowing only legitimate traffic to pass. Content Delivery Networks (CDNs) help absorb traffic surges by distributing load worldwide. Combining these approaches enhances resilience and reduces single points of failure during an attack.
The Role of Cloud and CDN Providers in DDoS Defense
Cloud and Content Delivery Network (CDN) providers play vital roles in protecting clients from DDoS attacks. Their distributed network infrastructure naturally absorbs and disperses large volumes of traffic, diluting the attack’s effectiveness. Additionally, these providers often offer integrated security services, including DDoS mitigation, real-time traffic inspection, and automatic rerouting. By leveraging vast network resources and advanced analytics, cloud and CDN providers can respond rapidly to emerging threats, enabling businesses to maintain uptime without investing heavily in in-house infrastructure. Many companies now rely on these services as a cost-effective and scalable defense solution.
Legal and Ethical Considerations Surrounding DDoS
Engaging in DDoS attacks is illegal in most jurisdictions worldwide, with perpetrators facing criminal charges, severe fines, and imprisonment. However, enforcement presents challenges due to the attackers’ use of anonymizing technologies and distributed infrastructure. Ethically, DDoS attacks disrupt not just intended targets but also innocent users who depend on the service. The emergence of “booter” or “stresser” services, which offer DDoS attacks for hire, poses additional legal and moral quandaries. Combating these illegal services and prosecuting offenders requires international cooperation, as cybercriminals often operate across borders in legal grey zones.
Preparing for the Future: Emerging Trends in DDoS Attacks and Defense
As technology evolves, so do the tools and tactics used in DDoS attacks. The proliferation of IoT devices means that botnets may grow more powerful, with attackers increasingly targeting cloud-native applications. Meanwhile, attackers are leveraging artificial intelligence to create more adaptive and harder-to-detect attacks. On the defense side, developments in machine learning are enhancing automated detection and response, while blockchain-based solutions offer promising avenues for improved network trust and resilience. Organizations must adopt proactive strategies, regularly updating security postures and investing in threat intelligence sharing to stay ahead in this ever-changing landscape.
Conclusion
Distributed Denial of Service attacks remain a formidable challenge in the cybersecurity realm, capable of inflicting significant operational and financial damage across industries. Understanding the mechanisms behind DDoS attacks, the motivations fueling them, and the evolving tactics used by adversaries is crucial in crafting effective defense strategies. From detecting early warning signs to deploying layered mitigation techniques and leveraging cloud-based solutions, preparedness is the best defense. As cyber threats continue to grow in sophistication, fostering a culture of continuous vigilance, collaboration, and innovation will be essential to safeguarding digital infrastructure in the years ahead.
 Big O Notation Explained for Beginners
Big O Notation Explained for Beginners
 AI in Gaming: Smarter NPCs and Environments
AI in Gaming: Smarter NPCs and Environments
 Understanding Bias in AI Algorithms
Understanding Bias in AI Algorithms
 Introduction to Chatbots and Conversational AI
Introduction to Chatbots and Conversational AI
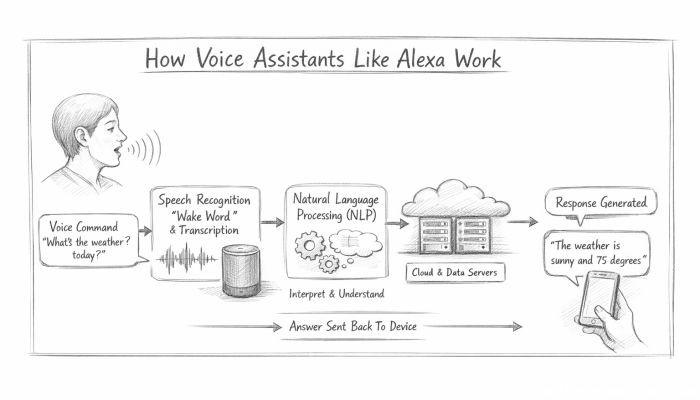 How Voice Assistants Like Alexa Work
How Voice Assistants Like Alexa Work
 Federated Learning: AI Without Sharing Data
Federated Learning: AI Without Sharing Data